
Founder | CTO | Influencer | Leader | Executive | CyberSecurity, Blockchain, AI, FinTech Advisory, Speaker & Trainer
Ramy AlDamati is a Cybersecurity & Blockchain expert holding master’s degrees in Information Security from the University of Hertfordshire. He has 17 years’ experience in the field with a strong focus on smart and resource-efficient systems. During those years, he has worked in multiple International CyberSecurity vendors like ( PaloAlto Network, FireEye & Kaspersky Lab ). Presently, he works as Chief Technology Officer at GloryThink Group and is involved in several research collaborations with international Blockchain & Financial Entities or ACADEMIC partners.
Experienced Chief Technology Officer with a demonstrated history of working in the information technology and services industry. Skilled in Negotiation, Business Planning, IT Service Management, Pre-sales, and Start-ups. Strong Techno-business development professional.
a Founder for (TrustyCrypto) an Ecosystm to make cypro world safe and secured.
Mixed Experience in CyberSecurity & Emerging Technology, engaged in many positions for mentoring, selling, business growth, research and many area.
Delivered multiple Training (English and Arabic) in AI, Bitcoin, Blockchain, Cryptocurrency, Distributed Ledger Technology, ICO, STO, Blockchain Protection & Cybersecurity, or many other topics for this domain.
He was able to deliver them in both languages (AR & EN) for many local and international organizations to help to raise awareness to all levels of people.
Available For: Authoring, Consulting, Influencing, Speaking
Travels From: Dubai
Speaking Topics: AI,Big Data,Blockchain,Business Strategy,Cryptocurrency,Cybersecurity,Digital Disruption,Digital Transformation,Edtech,Emerging Technology, Entreprene
| Ramy AlDamati | Points |
|---|---|
| Academic | 180 |
| Author | 37 |
| Influencer | 183 |
| Speaker | 70 |
| Entrepreneur | 140 |
| Total | 610 |
Points based upon Thinkers360 patent-pending algorithm.
 Cisco Routing and Switching Sales Certification
Cisco Routing and Switching Sales Certification
Tags: Cybersecurity, Emerging Technology, EdTech
 Cisco Security Sales Specialist
Cisco Security Sales Specialist
Tags: Cybersecurity, Emerging Technology, EdTech
 ISACA Certificate
ISACA Certificate
Tags: Cybersecurity, Emerging Technology, EdTech
 CompTIA Security+
CompTIA Security+
Tags: Cybersecurity, Emerging Technology, EdTech
 CompTIA Project+
CompTIA Project+
Tags: Emerging Technology, Management, EdTech
 Computer Hacking Forensic Investigator Certification - v3
Computer Hacking Forensic Investigator Certification - v3
Tags: Cybersecurity, Emerging Technology, EdTech
 CEH: Certified Ethical Hacker v6
CEH: Certified Ethical Hacker v6
Tags: Cybersecurity, Emerging Technology, EdTech
 ITIL Foundation v3
ITIL Foundation v3
Tags: Cybersecurity, Emerging Technology, EdTech
 Juniper Networks Certification Program (JNCP) - JNCIA
Juniper Networks Certification Program (JNCP) - JNCIA
Tags: Cybersecurity, Emerging Technology, EdTech
 Business Continuity (BS25999) Program Cert
Business Continuity (BS25999) Program Cert
Tags: Cybersecurity, Emerging Technology, EdTech
 ArcSight Certified Security Analyst (ASCA)
ArcSight Certified Security Analyst (ASCA)
Tags: Cybersecurity, Emerging Technology, EdTech
 Riverbed Certified Solutions Associate (RCSA)
Riverbed Certified Solutions Associate (RCSA)
Tags: Cybersecurity, Emerging Technology, EdTech
 CCNP (Cisco Certified Network Professional )
CCNP (Cisco Certified Network Professional )
Tags: Cybersecurity, Emerging Technology, EdTech
 CCNA (Cisco Certified Network Associate)
CCNA (Cisco Certified Network Associate)
Tags: Cybersecurity, Emerging Technology, EdTech
 PMP Certificate
PMP Certificate
Tags: Emerging Technology, Management, EdTech
 Microsoft Certified Solutions Expert (MCSE)
Microsoft Certified Solutions Expert (MCSE)
Tags: Cybersecurity, Emerging Technology, EdTech
 Microsoft Certified Solutions Associate (MCSA)
Microsoft Certified Solutions Associate (MCSA)
Tags: Cybersecurity, Emerging Technology, EdTech
 Microsoft Certified Professional (MCP)
Microsoft Certified Professional (MCP)
Tags: Cybersecurity, Emerging Technology, EdTech
 Technical Advisory Board Member
Technical Advisory Board Member
Tags: Blockchain, Cybersecurity, Emerging Technology
 Expert Advice On How To Handle Cyber Attacks
Expert Advice On How To Handle Cyber Attacks
Tags: Blockchain, Cybersecurity, Emerging Technology
 Share. Tweet. Protect. Repeat. - social media, the safe way
Share. Tweet. Protect. Repeat. - social media, the safe way
Tags: Cybersecurity, Emerging Technology, Privacy
 Keep cyber criminals out of your inbox for good. Here’s how
Keep cyber criminals out of your inbox for good. Here’s how
Tags: Cybersecurity, Privacy
 Are you protected from cyber attacks delivered via Wi-fi?
Are you protected from cyber attacks delivered via Wi-fi?
Tags: Cybersecurity, Privacy
 Member in Government Blockchain Association - GBA
Member in Government Blockchain Association - GBA
Tags: Blockchain, FinTech, Leadership
 Founder
Founder
Tags: Blockchain, Cryptocurrency, Cybersecurity
 Founder
Founder
Tags: Blockchain, Cryptocurrency, Startups
 The 5th National Cybersecurity Drill - Oman
The 5th National Cybersecurity Drill - Oman
Tags: Cybersecurity, Digital Transformation, Risk Management
 Certificate of appreciation to attend and speak in 10th Info Security Conference 2018
Certificate of appreciation to attend and speak in 10th Info Security Conference 2018
Tags: Cybersecurity, Emerging Technology, Entrepreneurship
 ARAMCO ISA Workshop 2018
ARAMCO ISA Workshop 2018
Tags: Cybersecurity, Emerging Technology, Entrepreneurship
 Info Security Top Ambassador 2018 (ISNR AUH)
Info Security Top Ambassador 2018 (ISNR AUH)
Tags: Cybersecurity, Emerging Technology, Entrepreneurship
 ARAMCO ISA Workshop 2017
ARAMCO ISA Workshop 2017
Tags: Cybersecurity, Emerging Technology, Entrepreneurship
 MENA InfoSec Conference 2017
MENA InfoSec Conference 2017
Tags: Cybersecurity, Emerging Technology, Entrepreneurship
 KIPS eGov Champion 2017
KIPS eGov Champion 2017
Tags: Cybersecurity, Emerging Technology, Entrepreneurship
 Company Teamwork
Company Teamwork
Tags: Cybersecurity, Leadership, Business Strategy
 Building a Great Partner Community
Building a Great Partner Community
Tags: Cybersecurity, Leadership, Business Strategy
 EMEA SE Award Q12015 - Above & Beyond
EMEA SE Award Q12015 - Above & Beyond
Tags: Cybersecurity, Leadership, Business Strategy
 Flare award : EMEA SE High Achievement
Flare award : EMEA SE High Achievement
Tags: Cybersecurity, Leadership, Business Strategy
 3rd Forum Innovation & Entrepreneurship 2018
3rd Forum Innovation & Entrepreneurship 2018
Tags: Cybersecurity, Emerging Technology, Entrepreneurship
 Kaspersky CyberSecurity Weekend 2019
Kaspersky CyberSecurity Weekend 2019
Tags: Cybersecurity, Emerging Technology, Entrepreneurship
 KIACS 2019 ( 4th Cybersecurity Conference )
KIACS 2019 ( 4th Cybersecurity Conference )
Tags: Cybersecurity, Emerging Technology, Entrepreneurship
 Arab EmTech and Startups Conference
Arab EmTech and Startups Conference
Tags: Blockchain, Emerging Technology, Innovation
 CyberSecurity & Cryptocurrency must be two faces of the same coin. How to manage the cybersecurity risks of cryptocurrency?
CyberSecurity & Cryptocurrency must be two faces of the same coin. How to manage the cybersecurity risks of cryptocurrency?
Tags: Cryptocurrency, Cybersecurity, Risk Management
 Smart Contract Privacy Protection using AI in Cyber-Physical Systems: Tools, Techniques and Challenges
Smart Contract Privacy Protection using AI in Cyber-Physical Systems: Tools, Techniques and Challenges
Tags: AI, Cryptocurrency, Cybersecurity
Tags: Blockchain, Cybersecurity, EdTech

Tags: Blockchain, Cybersecurity, Leadership

Tags: Blockchain, Cryptocurrency, Digital Transformation

Tags: Cloud, Cybersecurity, Digital Transformation

Tags: Cybersecurity, Privacy
 Explore the new technology and its potential in mena region
Explore the new technology and its potential in mena region
Tags: Emerging Technology, Innovation, Leadership

Tags: Cybersecurity, Management, 5G
 An Interview with CTO of Glory Think Group, Ramy AlDamati
An Interview with CTO of Glory Think Group, Ramy AlDamati
Tags: AI, Leadership, Marketing
 Why blockchain is worth the hype
Why blockchain is worth the hype
Tags: Blockchain, Cryptocurrency, IoT
 Securing the Crypto Economy
Securing the Crypto Economy
Tags: Cryptocurrency, Cybersecurity, Leadership

Tags: Cybersecurity, Business Strategy, Business Continuity

Tags: Cybersecurity, Leadership, Business Continuity

Tags: Blockchain, Cybersecurity, Emerging Technology

Tags: Blockchain, Cybersecurity, Emerging Technology

Tags: Blockchain, Cybersecurity, Emerging Technology

Tags: Blockchain, Cybersecurity, Emerging Technology

Tags: Cybersecurity, Management, Leadership
Tags: Cryptocurrency, Cybersecurity, Emerging Technology
 Artificial Intelligence for Business
Artificial Intelligence for Business
Tags: AI, Digital Transformation

Tags: Blockchain, Cybersecurity, Emerging Technology
 These Tips Will Bolster Your Cybersecurity Efforts
These Tips Will Bolster Your Cybersecurity Efforts
Tags: Cybersecurity, Emerging Technology, Entrepreneurship
 How we can tackle the growing cybersecurity skills gaps ?
How we can tackle the growing cybersecurity skills gaps ?
Tags: Cybersecurity, Emerging Technology, Entrepreneurship
 Why Too many organizations make critical mistakes when embarking on large-scale digital transformation for their organization ?
Why Too many organizations make critical mistakes when embarking on large-scale digital transformation for their organization ?
Tags: Cybersecurity, Digital Transformation, EdTech
 Innovative Business & Digital Transformation Advising & Consulting
Innovative Business & Digital Transformation Advising & Consulting
Location: Virtual, Worldwide Fees: Hourly, Retainer, Proj. based
Service Type: Service Offered
 Authoring a various article on Industry 4.0 / AI / IoT / Cybersecurity / Digital Transformation / Blockchain / Cryptocurrency
Authoring a various article on Industry 4.0 / AI / IoT / Cybersecurity / Digital Transformation / Blockchain / Cryptocurrency
Location: Virtual Fees: $150
Service Type: Service Offered
 ARAMCO ISA Workshop 2018
ARAMCO ISA Workshop 2018
Location: Aramco KSA Date : April 12, 2018 - April 12, 2018 Organizer: Aramco KSA
 Certificate of appreciation to attend and speak in 10th Info Security Conference 2018
Certificate of appreciation to attend and speak in 10th Info Security Conference 2018
Location: Kuwait Date : May 09, 2018 - May 10, 2018 Organizer: KAIT
 IGA Bahrain - Cyber Hawks Day Event - Bahrain/Manama
IGA Bahrain - Cyber Hawks Day Event - Bahrain/Manama
Location: Bahrain/Manama Date : October 05, 2017 - October 05, 2017 Organizer: IGA Bahrain
 The 4th Kuwait Industrial Automation & Control Systems Conference
The 4th Kuwait Industrial Automation & Control Systems Conference
Location: Kuwait Date : December 01, 2019 - December 02, 2019 Organizer: Kuwait Oil Company & Kuwait Petroleum
 The Gartner Security & Risk Management Summit in Dubai
The Gartner Security & Risk Management Summit in Dubai
Location: Dubai, UAE Date : October 28, 2019 - October 28, 2019 Organizer: Gartner
 The ITA Oman 5th edition of National CyberSecurity Drill Days in Muscut, Oman
The ITA Oman 5th edition of National CyberSecurity Drill Days in Muscut, Oman
Location: Muscut, Oman Date : September 09, 2019 - September 11, 2019 Organizer: Information Technology Authority - Oman , International Telecommunication Union Regional CyberSecur
 Monthly session for ISACA Amman Chapter
Monthly session for ISACA Amman Chapter
Location: Amman - KPMG Academy - Shmeisani Date : July 29, 2019 - July 29, 2019 Organizer: ISACA Amman Chapter
 Kaspersky 3. Siber Güvenlik Zirvesi - Ankara - 15.05.2018
Kaspersky 3. Siber Güvenlik Zirvesi - Ankara - 15.05.2018
Location: Ankara , Turkey Date : May 15, 2018 - May 15, 2018 Organizer: Siber Güvenlik Zirvesi & Kaspersky Lab Tukey
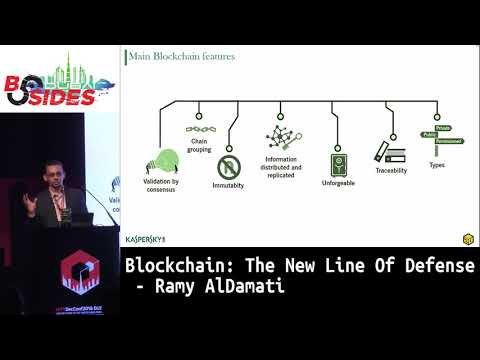
 BSides Dubai 2018: Blockchain: The New Line Of Defense - Ramy AlDamati
BSides Dubai 2018: Blockchain: The New Line Of Defense - Ramy AlDamati
Location: Dubai Date : December 25, 2018 - December 25, 2018 Organizer: BSides Dubai
 Cloud & Security Summit 2017
Cloud & Security Summit 2017
Location: Dubai Date : January 23, 2017 - January 23, 2017 Organizer: Ingram Micro Cyber Security
 Digital Banking and Security Conference , Baku, Azerbizan
Digital Banking and Security Conference , Baku, Azerbizan
Location: Baku, Azerbizan Date : May 14, 2018 - May 14, 2018 Organizer: FA International Trade Events
 Kuwait Digital Transformation Conference -
Kuwait Digital Transformation Conference -
Location: Radisson Blu Hotel, Kuwait Date : November 28, 2018 - November 29, 2018 Organizer: kuwaitdx
 FinTech Program Facilitator/Trainer
FinTech Program Facilitator/Trainer
Location: Amity University Dubai Campus Date : December 01, 2019 - June 30, 2020 Organizer: Amity University Dubai
 Gartner Security & Risk Management Summit
Gartner Security & Risk Management Summit
Location: Dubai, UAE Date : October 27, 2019 - October 28, 2019 Organizer: Gartner Security & Risk Management Summit
 Cyber Defense Summit
Cyber Defense Summit
Location: Saudi Arabia - Riyadh Date : February 13, 2019 - February 15, 2019 Organizer: Riyadh International Convention & Exhibition Center
 BSIDES , HITBSecConf2018 - Dubai ( BLOCKCHAIN: THE NEW LINE OF DEFENSE)
BSIDES , HITBSecConf2018 - Dubai ( BLOCKCHAIN: THE NEW LINE OF DEFENSE)
Location: Grand Hyatt Dubai, United Arab Emirates Date : November 27, 2018 - November 27, 2018 Organizer: HITB Security
 Arab EmTech & Startups Conference
Arab EmTech & Startups Conference
Location: Virtual Date : November 16, 2020 - November 18, 2020 Organizer: Arab EmTech & Startups Conference
 Explore the new technology and its potential in mena region
Explore the new technology and its potential in mena region
Location: Virtual Date : November 08, 2020 - November 08, 2020 Organizer: MANinaCUBE
 ARAB EmTech & startups Virtual FREE Conference
ARAB EmTech & startups Virtual FREE Conference
Location: Online Date : November 16, 2020 - November 18, 2020 Organizer: ARAB EmTech & startups Conference
 Blockchain & Fintech Digital Summit 2020
Blockchain & Fintech Digital Summit 2020
Location: https://events.marketsandmarkets.com/marketsandmarets-blockchain-and-fintech-digital-summit/ Date : May 28, 2020 - May 29, 2020 Organizer: MarketsandMarkets Research Private Ltd.
 CyberSecurity for Blockchain Technology
CyberSecurity for Blockchain Technology
Location: Online Date : April 28, 2020 - May 30, 2020 Organizer: ISACA Amman Chapter
 Live Course & Demo ( Blockchain Essentials )
Live Course & Demo ( Blockchain Essentials )
Location: Online Date : May 06, 2020 - May 06, 2020 Organizer: Amity University - Dubai
 Online Session about "Cyber Security Challenges for Blockchain".
Online Session about "Cyber Security Challenges for Blockchain".
Location: Online Date : May 09, 2020 - May 16, 2020 Organizer: MENA Blockchain