
CEO Cyber Eagle. Chairman of National Artificial Intelligence and Cyber Security ISAO, Chairman The Tortora Brayda Institute for AI & Cybersecurity, a global Think Tank to improve the effectiveness of partnerships in the private and public sectors. The ISAO aligns with Government Cyber policy and supports Cyber diplomacy and private sector growth within the NATO community.
Judge on United Nations' AI for Good Innovation Factory for North America and also Global Contest, 2020-2023. Selected as Judge for the new AI for Good Contest for Climate Change in partnership with ITU, UNESCO, FAO, IAEA, and World Bank at COP 28.
Former CEO of Gorilla Corporation, the leading global partner marketing and sales agency for the technology sector. Gorilla drives hundreds of millions of dollars annually for its vendor clients.
Special Constituent Member of the World Economic Forum and an expert contributor to the G20 for Global Risk Assessment.
Fellow of the British Computer Society, Freeman of the City of London, and a Hidalgo d'España.
Global Leader for the Forbes Technology Council Cybersecurity Group and contributes thought leadership articles on channel strategy, cybersecurity, and AI. Won two Forbes recognition awards in 2023, and one in 2024. https://councils.forbes.com/u/15e589e1-5251-4b45-a03c-1c662051d440
https://twitter.com/tortorabrayda
https://www.youtube.com/@tortorabraydainstitute/videos
Available For: Advising, Authoring, Consulting, Influencing, Speaking
Travels From: Barcelona, London, Paris
Speaking Topics: AI, Technology Scale Up, Partner Strategy, Cybersecurity, Metaverse
| Carlo Tortora Brayda | Points |
|---|---|
| Academic | 0 |
| Author | 352 |
| Influencer | 213 |
| Speaker | 76 |
| Entrepreneur | 0 |
| Total | 641 |
Points based upon Thinkers360 patent-pending algorithm.
Tags: Climate Change, Cybersecurity, National Security
 The Neuro-Intuitive Frontier: How Cybersecurity Will Interface Into The Human Mind
The Neuro-Intuitive Frontier: How Cybersecurity Will Interface Into The Human Mind
Tags: Agentic AI, AI, Cybersecurity
 From Capacity to Resilience: How AI and Cybersecurity Are Redefining Infrastructure in in the Years Ahead
From Capacity to Resilience: How AI and Cybersecurity Are Redefining Infrastructure in in the Years Ahead
Tags: Agentic AI, AI, Cybersecurity
 Biological Computing and the Coming Disruption of AI
Biological Computing and the Coming Disruption of AI
Tags: AI, Business Strategy, Cybersecurity
 Polymorphic Defense: Cybersecurity For An AI-Driven Threat Landscape
Polymorphic Defense: Cybersecurity For An AI-Driven Threat Landscape
Tags: Agentic AI, AI, Cybersecurity
 Agentic AI Vs. AI Agents: Shaping The Future Of Cybersecurity
Agentic AI Vs. AI Agents: Shaping The Future Of Cybersecurity
Tags: Agentic AI, AI, Cybersecurity
 Beyond the Solid: "Reweaving Reality in a Quantum Universe"
Beyond the Solid: "Reweaving Reality in a Quantum Universe"
Tags: Culture, Leadership, Management
 Beyond the Clock: How Physics and Consciousness Are Rewriting the Nature of Time
Beyond the Clock: How Physics and Consciousness Are Rewriting the Nature of Time
Tags: Culture, Leadership, Quantum Computing
 When Might We Achieve a 300 Logical Qubit Quantum Computer? A Forward-Looking Perspective
When Might We Achieve a 300 Logical Qubit Quantum Computer? A Forward-Looking Perspective
Tags: AI, Business Strategy, Quantum Computing
 Transcendent Leadership: How Understanding Consciousness Elevates Business
Transcendent Leadership: How Understanding Consciousness Elevates Business
Tags: Business Strategy, Culture, Leadership
 The Moral Hacker: Building Your Tech Brand Without Selling Your Soul
The Moral Hacker: Building Your Tech Brand Without Selling Your Soul
Tags: Business Strategy, Culture, Cybersecurity
 Improving Cyber Readiness In The Age Of AI And Quantum Computing
Improving Cyber Readiness In The Age Of AI And Quantum Computing
Tags: AI, Cybersecurity, Quantum Computing
 Reimagining Democracy Through Artificial Intelligence
Reimagining Democracy Through Artificial Intelligence
Tags: AI, GovTech, National Security
 Harnessing AI For Your Company’s ESG Strategy
Harnessing AI For Your Company’s ESG Strategy
Tags: AI, Digital Transformation, Sustainability
 12 Cybersecurity Measures To Defend Against The Rise Of AI And Quantum Computing
12 Cybersecurity Measures To Defend Against The Rise Of AI And Quantum Computing
Tags: AI, Cybersecurity, Quantum Computing
 20 Trends In Leveraging Technology For Cyber And Physical Security
20 Trends In Leveraging Technology For Cyber And Physical Security
Tags: AI, Cybersecurity, Emerging Technology
 The Huge Task Of Building Safety Into The Metaverse
The Huge Task Of Building Safety Into The Metaverse
Tags: AR/VR, Cybersecurity, Metaverse
 Mitigating AI-Based Cyberattacks
Mitigating AI-Based Cyberattacks
Tags: AI, Cybersecurity, Generative AI
 12 Critical Steps To Safeguard Your Company From Cyberattacks
12 Critical Steps To Safeguard Your Company From Cyberattacks
Tags: AI, Business Strategy, Cybersecurity
 The Vulnerability Of Mid-Market Critical Infrastructure Against Cyberattacks And Why It Matters
The Vulnerability Of Mid-Market Critical Infrastructure Against Cyberattacks And Why It Matters
Tags: Cybersecurity, Leadership, National Security
 How To Move Your Technology Channel Partner To The Subscription Model
How To Move Your Technology Channel Partner To The Subscription Model
Tags: Business Strategy, Digital Transformation, Management
 The Importance Of Broadening Your Channel Partner Ecosystems
The Importance Of Broadening Your Channel Partner Ecosystems
Tags: Business Strategy, Digital Transformation, Ecosystems
 2017 Sales Plan
2017 Sales Plan
Tags: AI, Cybersecurity, Emerging Technology
 5 Things vendors and partners should know about Pure Storage
5 Things vendors and partners should know about Pure Storage
Tags: AI, Cybersecurity
 5 Things Vendors and Channel need to know about DELL
5 Things Vendors and Channel need to know about DELL
Tags: AI, Cybersecurity, Sustainability
 When Intuition Becomes Infrastructure: The Cognitive Frontier of Cybersecurity
When Intuition Becomes Infrastructure: The Cognitive Frontier of Cybersecurity
Tags: AI, Cybersecurity, Sustainability
 The Vertical Now
The Vertical Now
Tags: AI, Cybersecurity, Sustainability
 Polymorphic Defense: A Doctrinal Leap in Cybersecurity Strategy for an AI-Driven Threat Landscape
Polymorphic Defense: A Doctrinal Leap in Cybersecurity Strategy for an AI-Driven Threat Landscape
Tags: AI, Cybersecurity, Sustainability
 Agentic AI Vs. AI Agents: Shaping The Future Of Cybersecurity
Agentic AI Vs. AI Agents: Shaping The Future Of Cybersecurity
Tags: AI, Cybersecurity, Sustainability
 Beyond the Solid: "Reweaving Reality in a Quantum Universe"
Beyond the Solid: "Reweaving Reality in a Quantum Universe"
Tags: AI, Cybersecurity, Sustainability
 Six Considerations For Successful Business Partnering
Six Considerations For Successful Business Partnering
Tags: AI, Cybersecurity, Sustainability
 Seamless: Successful B2B Marketing, Selling, and Account Management
Seamless: Successful B2B Marketing, Selling, and Account Management
Tags: Leadership, Marketing, Sales
 Cybersecurity Measures to Defend Against the Rise of AI and Quantum Computing
Cybersecurity Measures to Defend Against the Rise of AI and Quantum Computing
Tags: AI, Cybersecurity, Quantum Computing
 Building bridges: Public-private partnerships for an equitable AI future
Building bridges: Public-private partnerships for an equitable AI future
Tags: AI, Digital Transformation, Sustainability
 Cyber Eagle. Safeguarding Critical Infrastructure with AI and Private Public Partnerships.
Cyber Eagle. Safeguarding Critical Infrastructure with AI and Private Public Partnerships.
Tags: AI, Cybersecurity, National Security
 17 Trending Business Topics That Need A CTO’s Perspective
17 Trending Business Topics That Need A CTO’s Perspective
Tags: AI, Cybersecurity, Sustainability
Tags: AI, AI Ethics, Sustainability
 Cybersecurity’s Missing Layer: From Alerts to Real-Time Control in an AI and Quantum Era
Cybersecurity’s Missing Layer: From Alerts to Real-Time Control in an AI and Quantum Era
Tags: Agentic AI, Cybersecurity, Quantum Computing
Tags: Agentic AI, AI, Cybersecurity
Tags: Agentic AI, AI, Climate Change
 AI for Climate Innovation Factory 2025 live pitching session – 1st session
AI for Climate Innovation Factory 2025 live pitching session – 1st session
Tags: Agentic AI, AI, Climate Change

Tags: Agentic AI, AI, Cybersecurity
 Agentic AI: The Cybersecurity Game-Changer or Risk Multiplier?
Agentic AI: The Cybersecurity Game-Changer or Risk Multiplier?
Tags: Agentic AI, AI, Cybersecurity

Tags: AI, Cybersecurity, Entrepreneurship
 Cybersecurity Leadership in a World of Evolving Threats
Cybersecurity Leadership in a World of Evolving Threats
Tags: Cybersecurity, Leadership, National Security
 Identifying and scaling AI startups for SDGs ITU AI for Good Innovation Factory 2020-2024 Activities Report
Identifying and scaling AI startups for SDGs ITU AI for Good Innovation Factory 2020-2024 Activities Report
Tags: Agentic AI, AI, Sustainability
 A fireside chat with Carlo Tortora Brayda and Joe Sykora on Partner Ecosystems in Cybersecurity
A fireside chat with Carlo Tortora Brayda and Joe Sykora on Partner Ecosystems in Cybersecurity
Tags: Business Strategy, Change Management, Cybersecurity
 Ransomware: To Pay or not to Pay. A tale of moral dilemma.
Ransomware: To Pay or not to Pay. A tale of moral dilemma.
Tags: Cybersecurity, Digital Transformation, National Security

Tags: AI, Climate Change, Sustainability
 Building bridges: Public-private partnerships for an equitable AI future
Building bridges: Public-private partnerships for an equitable AI future
Tags: AI, Change Management, Cybersecurity
 A Chat with Carlo Tortora Brayda: Founder and Executive Chairman of Tortora Brayda Institute for AI & Cybersecurity; former Chair of Gorilla Corporation
A Chat with Carlo Tortora Brayda: Founder and Executive Chairman of Tortora Brayda Institute for AI & Cybersecurity; former Chair of Gorilla Corporation
Tags: Cybersecurity, Leadership, National Security
Tags: AI, Business Strategy, Cybersecurity

Tags: Business Strategy, Cybersecurity, Ecosystems

Tags: AI, Climate Change, Sustainability

Tags: AI, Business Strategy, Cybersecurity

Tags: AI, Climate Change, Sustainability


Tags: Sports



Tags: Innovation






Tags: Innovation

Tags: Sports




Tags: Business Strategy, Cybersecurity, Ecosystems
Tags: AI, Business Strategy, Cybersecurity
Tags: Business Strategy, Cybersecurity, IoT
Tags: AI, Business Strategy, Cybersecurity
Date : January 27, 2024
 AI-Driven Cloud Repatriation: Why Cybersecurity and Data Sovereignty Are Steering Companies Back to On-Premises Infrastructure
AI-Driven Cloud Repatriation: Why Cybersecurity and Data Sovereignty Are Steering Companies Back to On-Premises Infrastructure
We have seen significant movements in the tech industry since its inception. The launch of the IBM PC, the CRM revolution, Client/server, the Internet, Cloud, 5G, and AI.
This last one, however, is changing many things, including the balance between Cloud and on-premise deployments. We thought we had kissed data centers goodbye, and it was just the job of hyperscalers to deliver that functionality. Well, that is no longer the case.
Change is underway, driven by four primary factors related to AI: cost considerations, efficiency, security, and sovereignty. Society is retiring from a public Cloud only reality.
Welcome to Cloud Repatriation, the big trend of the next decade. As AI adoption accelerates, customers have no choice but to re-evaluate their infrastructure strategy. Control becomes more critical than ever as GRC (Governance, Risk, and Compliance) shifts from nebulous demands to complex realities backed by legislation and severe penalties for those who take such matters lightly. The allure of the Cloud is not what it once was: a one-size-fits-all miracle.
The writing was on the wall. Last year, 2024, a Barclays survey revealed that 83% of enterprise CIOs planned to repatriate workloads, a doubling on the previous year. Additionally, a 2024 Citrix survey confirmed that the level of Cloud repatriation is shockingly high, with 93% of respondents undertaking repatriation in a sample of 1,200 enterprises.
Generative and now agentic AI is the primary driver, and it is not just about cost reduction. It is about two critical drivers: sovereignty and cybersecurity.
Grandview Research, a leading research and analysis firm, states that the global AI market is set to rise at a 36.8% CAGR.
AI workloads are particularly demanding in terms of training, preparation, and deployment to the public. Public clouds carry the indeterminate risk in that it is difficult to predict costs until it's too late. Many data-focused enterprises have saved a considerable amount by repatriating cloud workloads and data. A noteworthy example is Dropbox, which saved $75 million this way.
GDPR and similar regulations underscore the need to repatriate Cloud Services. AI systems are often bathed in personally identifiable information (PII)—a compliance nightmare. Despite significant advancements in cybersecurity, Public Cloud remains a highly sought-after target for breaches.
A 2023 Thales survey reported that 45% of businesses experienced cloud data breaches. These risks are unacceptable in any critical infrastructure, especially in finance, banking, healthcare, military, power grids, and even in crypto and social media, where they become too hard to handle.
Cybersecurity is the primary reason for repatriating AI to the Cloud. With medical diagnostics, fraud prevention, and the risk of criminals hacking into operational technology (OT) systems and water treatment plants to poison water supplies, for instance, it is clear that cyber defense strategies need to change, even in their approach to infrastructure.
Despite the incredible investments cloud providers place in security, the shared responsibility model leaves customers accountable and transfers risk. Misconfigurations are a reality that is hard to shake off, and insider threats, alongside social engineering, will remain the most significant vector for crime until the day when all humans transcend greed and spite.
Most hyperscalers, AWS, Microsoft Azure, and Google Cloud, have invested heavily in security; however, the shared responsibility model leaves companies accountable for securing their digital assets. Misconfigurations, insider threats, and sophisticated social engineering continue to apply risks. In 2023, 95% of IT decision-makers reported a skills gap in cloud security, case in point.
On-premises solutions offer significantly more hands-on security control over the layout and configuration of your data, workloads, and application assets. You can, of course, tailor your firewalling and data encryption (use crypto agility) and, shortly, benefit from your very own Polymorphic Autonomous Cyber Defense. Customer data can remain ringfenced in your own LLM environment and on your data servers. HIPAA regulations are more comfortable with tightly controlled on-premises solutions. GDPR will not tolerate data migration across jurisdictions. All this is more controllable and guaranteed in-house, even though the accountability remains in force either way.
With new attack vectors such as model inversion and data poisoning. On-prem environments allow for nimbler isolation of exposed systems. Securing AI models, algorithms, and customer data becomes a non-negotiable imperative with zero tolerance for risk.
Data sovereignty refers to the principle that data should be stored and processed within the country or region of origin. Public clouds often rely on distributed data centers, which can make it challenging to prove compliance. As a result, companies frequently attempt to operate in a gray area. Sovereignty is a key prerogative, period.
Cloud repatriation activity varies by region, it is driven by dissimilarities in AI adoption and regulation. North America, with a 33.88% share of the global cloud AI market in 2024, leads in repatriation due to strict regulations such as HIPAA and CCPA, as well as a mature AI ecosystem.
The United States leads the global shift in repatriation due to regulations such as HIPAA and CCPA, as well as its relatively more mature AI ecosystem. According to Grandview Research, the USA accounts for almost 34% of the cloud market, which is likely driving the move towards repatriation.
In the Middle East and Asia, high AI adoption in India, combined with the imperative for sovereignty in the Gulf States, fuels the demand for on-premises infrastructure to meet stringent data sovereignty laws. Europe, where GDPR and data residency requirements are rigorous, is seeing growth in Cloud repatriation in larger countries, with an increasing number of large businesses moving cloud workloads back on-premises. Infrastructure providers are all seeing massive forecasted growth in AI Servers and HPC, particularly in AI Edge Computing Data Centers.
Cloud is evolving and will continue to play a central role in the tech stack, but AI is shifting the balance in a way many had not foreseen.
Most nations require Sovereign AI and Cybersecurity, and we need not only to adapt but to lead that charge if we want to grow.
Tags: Agentic AI, AI, Cybersecurity
 When Might We Achieve a 300 Logical Qubit Quantum Computer? A Forward-Looking Perspective
When Might We Achieve a 300 Logical Qubit Quantum Computer? A Forward-Looking Perspective
Imagine if every atom in the universe was retooled as a supercomputer. Not a modest step forward, but a breathtaking vault — solving in mere seconds what today’s finest machines would wrestle with for billions of years. That’s the promise of a quantum computer boasting 300 logical qubits. It’s a notion that stirs both wonder and urgency: how soon could this shift the ground beneath us, and what does it mean for those steering the course ahead?
Let’s unpack this together — no formulas required, just a shared curiosity about what’s on the horizon.
What Are Logical Qubits, Exactly?
In the familiar world of classical computing, bits are straightforward: a 1 or a 0, like flipping a switch. Quantum bits — qubits — play by stranger rules. They dance in a state of quantum superposition, embodying multiple possibilities at once. It’s as if they’re spinning coins, landing heads, tails, or hovering midair. This quirk lets them tackle vast arrays of outcomes simultaneously, but there’s a catch: they’re temperamental, prone to faltering under the slightest disturbance.
Logical qubits solve that problem. They’re the refined version — crafted from clusters of physical qubits and bolstered by intricate error-correction techniques. Think of them as seasoned professionals, dependable where their raw counterparts stumble. A system with 300 logical qubits would be a powerhouse ensemble, ready to confront challenges we’ve barely begun to imagine.
The Astonishing Reach of 300 Logical Qubits
Here’s where it gets jaw-dropping: a machine with 300 logical qubits could perform feats so immense that if every atom in the observable universe — every star, grain of sand, and wisp of gas — became a supercomputer, they’d still fall short. We’re talking an unfathomable scale of operations, compressing eons into moments. It’s not just about speed; it’s about rewriting what’s possible.
What might this unlock? Picture crafting pharmaceuticals by precisely modeling molecular interactions, or untangling global logistics snarls with a flick of computational wizardry. It’s the sort of breakthrough that doesn’t just refine our work — it redefines the questions we dare to ask.
The State of Play: Early 2025
So, where do we stand as of early 2025? The field’s alive with progress, driven by some of the sharpest minds out there:
We’re operating between 10 and 28 logical qubits now. To reach 300 requires a leap — 10 to 30 times the current count. Daunting, yes, but the pace of innovation suggests it’s within reach.
The Path Forward: Scaling the Quantum Frontier
Assembling logical qubits isn’t a simple stacking game — it’s more like orchestrating a symphony in a storm. Each logical qubit demands a supporting cast of physical ones, often 25 to 1,000, to fend off errors. Smarter designs aim to trim that ratio to 10–20, a shift that could make 300 logical qubits viable with 3,000–6,000 physical qubits. Here’s what the frontrunners are planning:
The AI Advantage: Accelerating Progress
Here’s an intriguing twist: artificial intelligence is stepping in as a partner. AI’s knack for refining error correction, optimizing designs, and streamlining processes could shave years — perhaps 3 to 10 — off the timeline. If it narrows that physical-to-logical ratio to 20:1, 6,000 physical qubits might suffice for 300 logical ones. Suddenly, the finish line feels closer than we thought.
A Timeline to Ponder
So, when might this milestone arrive? Let’s sketch out some possibilities:
My take? 2027–2031. I’d wager 100 logical qubits by 2027 is plausible, with 300 following by 2029, especially if AI keeps lending a hand. Too bold? Maybe, but the trends are hard to ignore.
Why This Matters to You
When a 300 logical qubit system comes online, it’ll reshape the landscape. It could unravel today’s encryption, pressing us to rethink security from the ground up. At the same time, it’ll open doors to marvels — new materials, climate solutions, you name it. For leaders, it’s a call to prepare, not just to watch.
As you gaze at the stars some evening, consider this: we’re crafting a tool that could outthink them all. It’s not a matter of if, but when. I’m betting on 2029, give or take a year or two. What will we do with that power when it’s ours to wield?
Tags: AI, Business Strategy, Quantum Computing
 Bridging the Divide: Securing the Promise of AI in a Less Developed World
Bridging the Divide: Securing the Promise of AI in a Less Developed World
The transformative potential of Artificial Intelligence (AI) is undeniable. From revolutionizing healthcare to optimizing logistics and personalizing education, AI holds the key to unlocking a brighter future for all. However the reality in many less developed countries (LDCs) is very different. The transformational benefits that AI could bring to enable poorer countries to leapfrog to a massively greater position of economic strength in relatively few decades could remain elusive unless there is an orchestrated effort. We are all stakeholders in this.
Creating a more efficient global economy benefits everyone and we all need to grow together.
This article is based on my personal experience in reducing the digital divide in Ethiopia and delves into the unique security concerns surrounding AI in LDCs. It highlights how existing inequalities can be exacerbated by biased data, limited resources, and a lack of awareness. These considerations are particularly nerve wracking when considering nations where civil dissent may be brewing often on ethnic grounds. The article further explores mitigation strategies, emphasizing the need for international collaboration, capacity building, and responsible AI development practices that bridge the digital divide and promote inclusive benefits.
The Digital Divide: A Breeding Ground for AI Security Risks
The digital divide refers to the gap between those who have access to information and communication technologies (ICTs) and those who don’t. The United Nations, ITU in particular, has been driving this point for a long time, justifiably as it is central to development, wealth, health and trade. Having said that, now that the Fourth Industrial Revolution, as Klaus Schwab, leader of the World Economic Forum, coined it, is well underway and it does bring about some real dangers that we must all be aware of so that we can help each other understand and mitigate them.
Building Bridges: Strategies for Inclusive AI Security in LDCs
Bridging the digital divide remains a crucial priority for the international community. The international organization community has been hard at work for many years but the problem is so massive that it is hard to tame.
Only through education can we foster trust in AI and mitigate the effects of bias, misinformation, and manipulation.
Conclusion: A Shared Responsibility for a Secure and Inclusive AI Future
The potential of AI to revolutionize the world is undeniable. But ensuring everyone gets a slice of the pie, not just the privileged few, requires a concerted effort. Developed nations and international organizations can’t afford to be bystanders. We all have a stake in creating a secure and inclusive AI future. Let’s roll up our sleeves, share knowledge, and build robust safeguards. Only through collaborative sweat can we ensure AI becomes a force for positive change, not just in a few select pockets but across the globe. After all, a rising tide lifts all boats, doesn’t it?
Tags: AI, Climate Change, Cybersecurity
 The Challenges of Making AI Equitable and How Partnerships Can Deliver
The Challenges of Making AI Equitable and How Partnerships Can Deliver
As humans, we’ve always straddled a delicate balance between going it alone and coming together as a collective. While individual ambition often pushes us forward, our real strength lies in teamwork—building, creating, and solving problems together. This capacity for collaboration has helped us thrive as a species, and now, it’s essential as we face one of the greatest challenges of our time: ensuring artificial intelligence (AI) serves everyone equally.
Making AI truly equitable isn’t just about better technology or clever algorithms. It’s about creating a system where everyone—no matter where they are or what resources they have—can access and benefit from this transformative technology. That’s where partnerships, particularly public-private partnerships (PPPs), come into play. But making these collaborations work requires more than just signing agreements. It takes commitment, alignment of goals, and a focus on long-term outcomes.
What Does Equity in AI Really Mean?
Equity isn’t just a buzzword; it’s about making sure everyone has what they need to succeed. In the context of AI, that means addressing the digital divide—a gap that’s especially glaring in developing nations. Millions of people around the world lack even the basics needed to participate in the digital age. These essentials include:
1. A device, such as a smartphone or computer.
2. The knowledge to use that device effectively.
3. Access to a reliable internet connection.
4. A stable source of electricity to power it all.
Even in places where smartphones are becoming more common, their use is often limited to making calls or sending messages. Many people don’t have the opportunity—or the means—to use these devices for more advanced tasks like browsing the web or engaging with AI tools. Without targeted efforts to close these gaps, the promise of AI will remain out of reach for billions.
Education is a crucial piece of the puzzle, especially for adults and older populations who’ve had little exposure to digital tools. At the same time, infrastructure outside urban areas remains a significant hurdle. Poor connectivity, unreliable electricity, and, in some cases, restrictive government policies prevent people from fully engaging with the digital world.
Why Bridging the Digital Divide Matters
Globally, a third of people are still offline. Among those who are connected, more than half experience slow or unreliable internet. This digital divide doesn’t just hold individuals back; it limits progress for entire societies. AI, as powerful as it is, can’t deliver its full benefits in a world where so many are left behind.
The consequences of ignoring these disparities go beyond technology. A growing gap in digital access threatens to widen the wealth divide, stoke social unrest, and deepen existing inequalities. Ensuring equitable access to AI isn’t just the right thing to do—it’s an economic and social imperative. By providing tools and opportunities for all, we can spark innovation, create new markets, and build a more stable, prosperous world.
The Language Barrier: An Overlooked Challenge
Even as AI systems become more sophisticated, language remains a significant barrier. Most large language models (LLMs) support major languages like English, Chinese, and Spanish, but they leave out more than half the world’s population. For those who speak languages not supported by these systems, interacting with AI can feel like an insurmountable challenge.
Developing LLMs for underrepresented languages is no easy task. Take Amharic, the national language of Ethiopia, as an example. The datasets available for training Amharic LLMs are thousands of times smaller than those for dominant languages, making the process costly and complex. On top of that, Amharic’s intricate grammar and unique alphabet add to the technical hurdles. Limited resources and tight national budgets in countries like Ethiopia further complicate these efforts.
How Public-Private Partnerships Can Help
Addressing these challenges requires collaboration on a massive scale. Public-private partnerships (PPPs) bring together governments, businesses, and NGOs to pool resources, expertise, and influence. While this model holds great promise, it’s not without its challenges.
Lessons from Ethiopia
A few years ago, I was involved in a PPP in Ethiopia that brought together the federal government, Microsoft, the regional government of Amhara, and the NGO Alchemy World. The project aimed to digitize education in remote areas and promote entrepreneurship.
The obstacles we faced were enormous. Many communities lacked basic infrastructure, and accessing email required a half-day journey by donkey to the nearest cyber café. In areas where unemployment was rampant and clean water was scarce, the idea of AI equity seemed almost laughable. Yet, the partnership delivered life-changing results. Thousands people were lifted out of poverty, gaining dignified work in the digital economy, while millions of children now have access to improved education through digitization.
This success didn’t come easily. It took years of persistent effort and coordination among all parties. The project worked because each partner remained committed to the long-term goal, even when progress was slow.
Why Many Partnerships Fail
Despite their potential, many PPPs fail. Why? Often, it comes down to misaligned goals and a lack of trust:
1. Governments may lack the political will to sustain initiatives beyond the short term, and corruption can derail even the best-laid plans.
2. Corporations, driven by profit, may pull out if results aren’t immediate.
3. NGOs and local organizations, focused on community impact, sometimes find their values clash with those of their corporate or governmental partners.
The key to overcoming these challenges lies in relationships. Successful partnerships are built on trust, mutual respect, and a recognition that everyone’s success is interconnected. It’s about more than signing contracts; it’s about building human connections—shaking hands, sharing meals, and staying in constant communication.
The Bigger Picture: AI for Good
One example of a successful global initiative is AI for Good, a program launched by the United Nations' International Telecommunications Union. This initiative encourages partnerships to use AI in addressing global challenges, from climate change to education. Entrepreneurs working on AI solutions for agriculture, disaster management, and healthcare are supported and celebrated.
Similarly, the Cyber Eagle Project is leveraging generative AI to tackle cybersecurity challenges within NATO’s member countries critical infrastructure sectors. By automating processes and creating partnerships between governments and private companies, the project is reshaping how cybersecurity is approached on a massive scale. These examples show what’s possible when resources and vision align.
Moving Forward: A Call to Action
The road to AI equity is long and full of obstacles, but the rewards are worth the effort. Public-private partnerships hold the key to bridging the digital divide and ensuring that AI benefits everyone. For these partnerships to succeed:
- All stakeholders must be willing to share accountability and align their goals.
- Corporations and governments need to commit to long-term investment, even when immediate returns aren’t guaranteed.
- NGOs and civil society groups must play a central role in driving these initiatives forward.
Our ability to collaborate has always been our greatest strength. Now, as we face the challenges and opportunities of the AI age, it’s more important than ever. By coming together with shared purpose and determination, we can create a future where technology serves all of humanity—not just a privileged few. The choice is ours.
Tags: AI, Cybersecurity, Diversity and Inclusion
 Fireside Chat: Ransomware: Effective counter strategies vs spitting into the wind
Fireside Chat: Ransomware: Effective counter strategies vs spitting into the wind
This infographic-rich presentation outlines thought leadership ideas and best practices for handling Ransomware situations. It is the outcome of a deep conversation with experts James Taliento, AFTDRK, Matthew Leidlein, DAR, and Guillermo Christensen, K&L Gates (ex-CIA, ex-Diplomat)
Tags: Cybersecurity, Leadership, Risk Management
 Bridging the Divide: Securing the Promise of AI in a Less Developed World
Bridging the Divide: Securing the Promise of AI in a Less Developed World
The transformative potential of Artificial Intelligence (AI) is undeniable. From revolutionizing healthcare to optimizing logistics and personalizing education, AI holds the key to unlocking a brighter future for all. However the reality in many less developed countries (LDCs) is very different. The transformational benefits that AI could bring to enable poorer countries to leapfrog to a massively greater position of economic strength in relatively few decades could remain elusive unless there is an orchestrated effort. We are all stakeholders in this.
Creating a more efficient global economy benefits everyone and we all need to grow together.
This article is based on my personal experience in reducing the digital divide in Ethiopia and delves into the unique security concerns surrounding AI in LDCs. It highlights how existing inequalities can be exacerbated by biased data, limited resources, and a lack of awareness. These considerations are particularly nerve wracking when considering nations where civil dissent may be brewing often on ethnic grounds. The article further explores mitigation strategies, emphasizing the need for international collaboration, capacity building, and responsible AI development practices that bridge the digital divide and promote inclusive benefits.
The Digital Divide: A Breeding Ground for AI Security Risks
The digital divide refers to the gap between those who have access to information and communication technologies (ICTs) and those who don't. The United Nations, ITU in particular has been driving this point for a long time, justifiably as it is central to development, wealth, health and trade. Having said that, now that the Fourth Industrial Revolution, as Klaus Schwab, leader of the World Economic Forum, coined it, is well underway and it does bring about some real dangers that we must all be aware of so that we can help each other understand and mitigate them.
Building Bridges: Strategies for Inclusive AI Security in LDCs
Bridging the digital divide remains a crucial priority for the international community. The international organization community has been hard at work for many years but the problem is so massive that it is hard to tame.
Only through education can we foster trust in AI and mitigate the effects of bias, misinformation, and manipulation.
Conclusion: A Shared Responsibility for a Secure and Inclusive AI Future
The potential of AI to revolutionize the world is undeniable. But ensuring everyone gets a slice of the pie, not just the privileged few, requires a concerted effort. Developed nations and international organizations can't afford to be bystanders. We all have a stake in creating a secure and inclusive AI future. Let's roll up our sleeves, share knowledge, and build robust safeguards. Only through collaborative sweat can we ensure AI becomes a force for positive change, not just in a few select pockets but across the globe. After all, a rising tide lifts all boats, doesn't it?
Tags: AI, Cybersecurity, Digital Transformation
 RESOLVING CRITICAL INFRASTRUCTURE CYBER DEFENSE THROUGH PRIVATE PUBLIC PARTNERSHIPS
RESOLVING CRITICAL INFRASTRUCTURE CYBER DEFENSE THROUGH PRIVATE PUBLIC PARTNERSHIPS
In recent months, our Nation’s national security agencies have issued urgent advisories and testified before Congress on State-sponsored cyber-attacks, sabotage, and vulnerabilities embedded in the connected technologies managing life-essential infrastructure (power, gas, water, communications, transportation) in our country. While Executive Orders and guidance to critical infrastructure owners are a tangible first step to galvanize public awareness and action, more must be done to unify efforts to mitigate cyber risk across all sectors of our economy and way of life. Cyber attacks on infrastructure directly threaten human safety and property. Cyber protections for operational technologies (OT) can no longer be considered an optional investment for C-suites and boardrooms weighing various business risks.
A Task Force of the Tortora Brayda Institute, in partnership with the Association of U.S. Cyber Forces and the National A.I. & Cybersecurity ISAO, convened a council of 30 subject matter experts and thought leaders in February 2024 to focus nonprofit efforts on developing private-public partnerships to rapidly and sustainably improve the cyber resilience of the U.S. critical infrastructure with particular emphasis on mid-size company contributions.
A national response to these compelling threats must include more than the top 20 organizations with existing resources in each critical infrastructure segment to invest in protections immediately. The thousands of small system service providers in each sector, in most cases operating with limited margins, must have access to funds from public resources or public-private partnerships to implement capabilities to mitigate cyber risk.
For example, a medium-sized ethanol manufacturer with 120 employees based out of Sacramento, California, is just as crucial for providing services to hospitals throughout the State as a Fortune 100 manufacturer based on the eventuality of resource scarcity. Our initial research indicates that up to 300,000 companies in the 100 to 5,000-employee segment may exist within the 16 critical infrastructure verticals in the United States. If we included NATO allies, the number would rise to more than 800,000.
Alycia Farrell, Executive Member of the Association of U.S. Cyber Forces (AUSCF) and Board Member for the Tortora Brayda Institute, works directly with small and medium-sized businesses within the Defense Industrial Base, where she is tracking cyber threats to critical infrastructure and various sectors of the U.S. supply chain. "The world of CMMC and the DIB is a microcosm of the larger issue impacting the overall US commercial industrial base. While DoD is implementing the CMMC certification process to try and get a handle on increasing cybersecurity practices and compliance, the efforts and costs associated with mandating these practices will increase the financial burden on these companies to the point where it will negatively impact our national security supply chain. These companies will seek support and assistance in completing the compliance, assessment, and audit processes.” According to data from the DoD, up to 350,000 companies in the Defense Industrial base supply chain and certainly 80,000 need to step up their audit process.
"We need to explore all options for leveraging technology, and especially A.I., to support these companies in achieving better overall cyber protection and the associated compliance scoring that reflects their improved cybersecurity posture,” the former Senate Appropriations Professional staffer added. “In addition, we ought to ensure that consultants, MSPs, and MSSPs are supported, enabled, and adequately certified, likely bringing the overall target of Project Cyber Eagle beneficiaries to well over 300,000.”
The current geopolitical situation presents an exceptional threat to the critical infrastructure of the United States and its allies. From State-sponsored malware placed in operational technology (OT) to sabotage essential utilities to actual attacks on small water systems across the country, the U.S. is no longer a sanctuary from foreign attacks. U.S. citizens are squarely in the crosshairs of adversaries wanting to coerce national policymakers. In particular, the midmarket is known to be especially vulnerable. The Biden Administration's Federal Cyber Security Strategy and related implementation plan emphasize the importance of securing critical infrastructure in its totality, not just the market leaders.
The National A.I. & Cybersecurity ISAO, part of the Tortora Brayda Institute, has studied this issue for 18 months. During this time, Institute leaders have been formulating solutions with members of the U.S. Government, academia, the private sector, and the NATO community to rapidly improve the cybersecurity posture of critical infrastructure.
Lucian Niemeyer, CEO of the national non-profit Building Cyber Security, with decades of experience as a former Assistant Secretary of Defense, former Senate Armed Services Committee staff Member and top defense official in the White House Office of Management and Budget, and Board Member of the Tortora Brayda Institute commented: "When do cyber sabotage and attacks by State sponsors cross the threshold of an act of war?” As an example, in partnership with the UK, Canada, and Australia, The Cybersecurity and Infrastructure Security Agency (CISA), National Security Agency (NSA), and Federal Bureau of Investigation (FBI) issued a Joint Advisory on February 7th, 2024 announcing that People's Republic of China (PRC) state-sponsored cyber actors are seeking to pre-position themselves on I.T. networks for disruptive or destructive cyberattacks against U.S. critical infrastructure in the event of a significant crisis or conflict with the United States.
"This is a direct act of cyber sabotage. We can't continue relying on the infrastructure operators to identify and fight back State-Sponsored attacks. We must unite all federal agencies under one lead entity with the responsibility and accountability to work with all private sector owners to close the gaps in the cyber protections of our national infrastructure at the federal, regional, State, and local levels. Continuing to rely on private companies for our Nation’s cyber defense will ultimately lead to a national catastrophe”.
The Cyber Eagle Project will commit resources and expertise in solutions to rapidly and effectively improve the cybersecurity posture of our critical industries.
Martin Hawley, Director at Angoka, a U.K. Operational Technology Cybersecurity vendor, remarked: "I think this idea has potential in the U.K., and insurers and accountancy firms could be good channels to market Cyber Eagle to get people involved.
The objectives are these:
The Cyber Eagle Project is formed around two core pillars: developing a technological framework and identifying funding opportunities. The workflow for the technological part involves generative AI-specialized chatbot outreach that will target the most appropriate people in each target company to serve them with a high-level cyber risk assessment similar to what will be provided by a Cyber Risk Assessment vendor, as well as a cyber exposure assessment of their risk on the dark web and restricted channels used by cybercriminals on platforms (e.g. Telegram.) To this effect, Mikko Niemela, CEO of Cyber Intelligence House, commented: ""I am pleased that our Cyber Exposure platform can contribute to the overall effort by providing companies in critical infrastructure with the benefit of ten years of research data collection in collaboration with INTERPOL, UNODC, and other reputable law enforcement agencies, on the explicit risk and specific vulnerabilities that companies face from cyber criminals. With generative AI, we can deliver a user-friendly summary and comparison of the current level of cybersecurity."
The next phase for the proactive generative A.I. chatbot would be to engage and recommend appropriate solutions based on the detected gap when measured against one or more standardization and compliance frameworks like NIST CSF or many others. Our A.I. engine will determine and validate the solutions by a cybersecurity professional.
Keeping data secure within the framework of the Cyber Eagle Project will be foundational, and security will be built into the AI across layers from DevSecOps upwards. Post-quantum encryption will be carefully considered, as will the newest and most effective homomorphic encryption algorithms.
The power and speed of enabling Generative AI to engage about 1 million technology professionals virtually simultaneously in critical infrastructure make Project Cyber Eagle a remarkable proposition.
The solution will be drawn from an ecosystem of 12 vendors and 500 partners focusing on the upper mid-market and another 18 vendors and 1000 partners aiming at the lower midmarket. These vendors would be selected on quality and complementarity criteria. We will construct a marketplace based on secure, reliable, and reputable marketplace technology vendors. The transactions would occur on this marketplace. The marketplace and the generative A.I. would ensure annual renewals and upgrades.
The second pillar is the funding element. One explored idea is providing forgivable loans for cybersecurity improvements through the Small Business Administration (SBA.) This could also be done through NIST. There are precedents for this type of funding. A company would need to be eligible for it. The funding agency would develop eligibility criteria. Companies could obtain the loan, implement the technology, upload the invoice, and have the loan forgiven.
FEMA and CISA, for instance, provide grants for tribal, State, and local governments. These programs need to be expanded and socialized more.
This end-to-end process would ensure the United States achieves unparalleled critical infrastructure security improvements in record time and could lead its allies to do the same.
Credits.
The following are all subject matter experts and Critical Infrastructure Task Force provisional members.
Co-Chairs
Steve DeSantis, Partner Ecosystems Sales Leader, Palo Alto Networks
Peter Hammermeister, Principal, Aligned Advisory Group
Michael Thiessmeier, Executive Director, National AI & Cybersecurity ISAO
Executive Members
Alycia Farrell, Executive Member, Association of US Cyber Forces
Joe Sykora, SVP Global Channels and Alliances, Proofpoint
Lucian Niemeyer, CEO of BuildingCyberSecurity.org
Miguel Garibay, VP of Operations and Administration
Dave Treadway, Founder EduGPT
David Mauro, Konica Minolta & Cybercrime Junkies
Jason Keller, Digital Strategy Director, Vistant
Gilles Esposito, Vice-Chair, Tortora Brayda Institute
Jill Wideman, Tortora Brayda Institute
Lucian Niemeyer, CEO Building Cyber Security
Mike Crandall, CEO Digital Beachhead
Laurin Groover, CEO The Groover Group, National Security, Cyber, Attorney
Mikko Niemela, CEO Cyber Intelligence House
Carlo Brayda, Executive Chairman Tortora Brayda Institute
Shaun Boggs, Director IT & Cybersecurity, Key Capture Energy
Tim Kapp, CEO CInco AI
Tony Zirnoon, CEO Human Capital Ventures
Krishna Priya, AI/ML Architect
Adnan Khaleel, Corporate Strategy Director, Intel
Lee Hibbert, Bamboo UK
Martin Hawley, Angoka UK
Marcus Fowler, CEO of Darktrace Federal
Guillermo Christensen, Partner KL Gates, National Security Lawyer
Chris Hadnagy, CEO Social Engineer LLC
Mary d’Angelo, Dark Web Threat Advisor, Search Light Cyber
Tags: AI, Cybersecurity, National Security
 Harnessing the Power of Green AI for Sustainability and Climate Change
Harnessing the Power of Green AI for Sustainability and Climate Change
COP 28 was the 28th Conference of the Parties to the U.N. Framework Convention on Climate Change in Dubai.
Most world leaders were present, as well as leaders of major corporations and NGOs around the world.
In an opening address to the COP28 U.N. climate summit, King Charles told world leaders the dangers of climate change were no longer a distant risk and urged them to take more action.
There was a clear sense of momentum in the air, and AI innovation was understood to help channel this energy into tangible solutions.
The time for action is ripe, and Green AI is the catalyst.
The United Nations Sustainable Development Goals are 17 strategic goals set to be achieved by 2030. Of these, the climate-specific ones that have been the focus of one of the side-events at COP 28 were the A.I. Crowdsourcing A.I. and Machine Learning, A.I. for Good Innovation Factory. The partners in this initiative were the International Telecommunication Union (ITU), the International Atomic Energy Agency (IAEA), the Food and Agriculture Organization (FAO), the United Nations Educational, Scientific and Cultural Organization (UNESCO), the Tortora Brayda Institute, and the U.S. National A.I. & Cybersecurity ISAO. The organizations converged to support ITU's A.I. for Good initiative geared toward AI/ML Innovation to combat climate change.
A.I. for Good Innovation Factory is a UN-led pitching platform to help startups thrive by connecting them into a multi-stakeholder support ecosystem and providing further support and guidance from within the U.N. This Climate Change edition of the contest is open to any innovative startups using A.I., and advanced algorithms and gives startups a global stage to promote their innovative solutions.
Five problems were identified for contestants to resolve through Green A.I. sustainability ideas:
The following companies made the final cut and were awarded an Award by United Nations Leaders during the COP 28 event.
Poseidon-AITM, headquartered in Singapore and led by Dr. Amaj Rahimi-Midani, addresses challenges in the rapidly expanding seafood farming industry, which constitutes nearly 50% of global seafood production. This initiative is critical for sustainable growth and efficient water resource use, especially given the implications of climate change on aquatic ecosystems. The industry faces three primary challenges: environmental changes due to climate change, expertise and knowledge deficits, and limited financial support. Poseidon-AITM harnesses IoT, A.I., and ML.
technologies to support farmers, indigenous groups, and vulnerable communities adapt to these challenges and advance sustainable development.
Using cost-effective IoT devices, Poseidon-AITM gathers real-time data from aquatic environments and soil. This data trains AI/ML algorithms to optimize feeding, growth rates, and maturity timing and monitor nitrate levels from fish waste. Additionally, image processing refines these algorithms to reflect real-world conditions.
This approach reduces production costs by 20%, and increases yield by 35%. The algorithms are integrated into Intelligent Aquaculture Systems modules, providing expert guidance for communities. Each module generates revenue and saves 2 tons of rainwater, contributing to nine Sustainable Development Goals.
Bloom Africa is a Ghanaian startup that utilizes cutting-edge A.I. technology, including Natural Language Processing and custom models, to deliver advanced analytics in agricultural systems, providing insights through natural language and employing AI-IoT for enhanced forecasting in the face of climate change challenges. Collaborating with FAO, Bloom Africa enhances Earth Map by introducing Clarice—an A.I. chat assistant capable of interacting with Earth Map using natural language. CEO Hamza Mohammed stated: "Our A.I. assistant, Sana, revolutionizes smart farming insights, seamlessly integrating with farm data and farm management systems and providing real-time expert guidance to propel the adoption of state-of-the-art farming practices."
S.I. Analytics aims to improve global climate interpretation and establish an early warning system with two innovative services: Georain and Geocloud. Yeji Choi, CEO, explains: "Georain offers effective precipitation monitoring using high-resolution geostationary satellite imagery analyzed by AI-based radar maps. By applying a generative deep learning model with physical constraints, SIA enhances accuracy in rain rate retrieval algorithms for geostationary satellites, overcoming limitations of continuous monitoring with limited LEO satellites".
Geocloud predicts future states of geostationary satellite imagery up to 20 hours. Applying deep learning to past observation data provides reliable predictions of future atmospheric states, excelling in short-term forecasts. Geocloud utilizes the Deterministic Guidance Diffusion Model, balancing deterministic and probabilistic forecasting methods.
Based on meteorological satellite and global model data, these services are accessible globally, benefiting underdeveloped countries with limited meteorological equipment.
Finapp is an A.I. technology based on Cosmic Ray Neutron Sensing.
Finapp supports precision agriculture by providing unique knowledge of soil moisture for better irrigation, efficient water use, and hunger eradication.
Cosmic rays from space and in contact with the Earth's atmosphere generate a cascade of particles, including fast neutrons, which interact mainly with water molecules. When they come into contact with water in the ground or snow, part of the fast neutrons is absorbed, and part is reflected into the air, losing part of the initial energy; thus, slow neutrons are born.
A significant difference between the number of fast and slow neutrons implies a large amount of water and vice versa. Since fast neutrons have enough energy to penetrate inside the ground for many cm (meters in snow), the given figure is representative in depth. Conversely, slow neutrons are distributed over large distances; it is possible to monitor the water content over vast areas, about 5 hectares at sea level up to 30 hectares at altitude.
The business community has already embraced A.I. for innovation and efficiency. Now, businesses need to recognize the immense potential of A.I. in advancing sustainability. By harnessing A.I.'s capabilities, companies can foster environmentally responsible practices, optimize resource consumption, and contribute to a more sustainable world.
Tags: AI, Climate Change, Sustainability
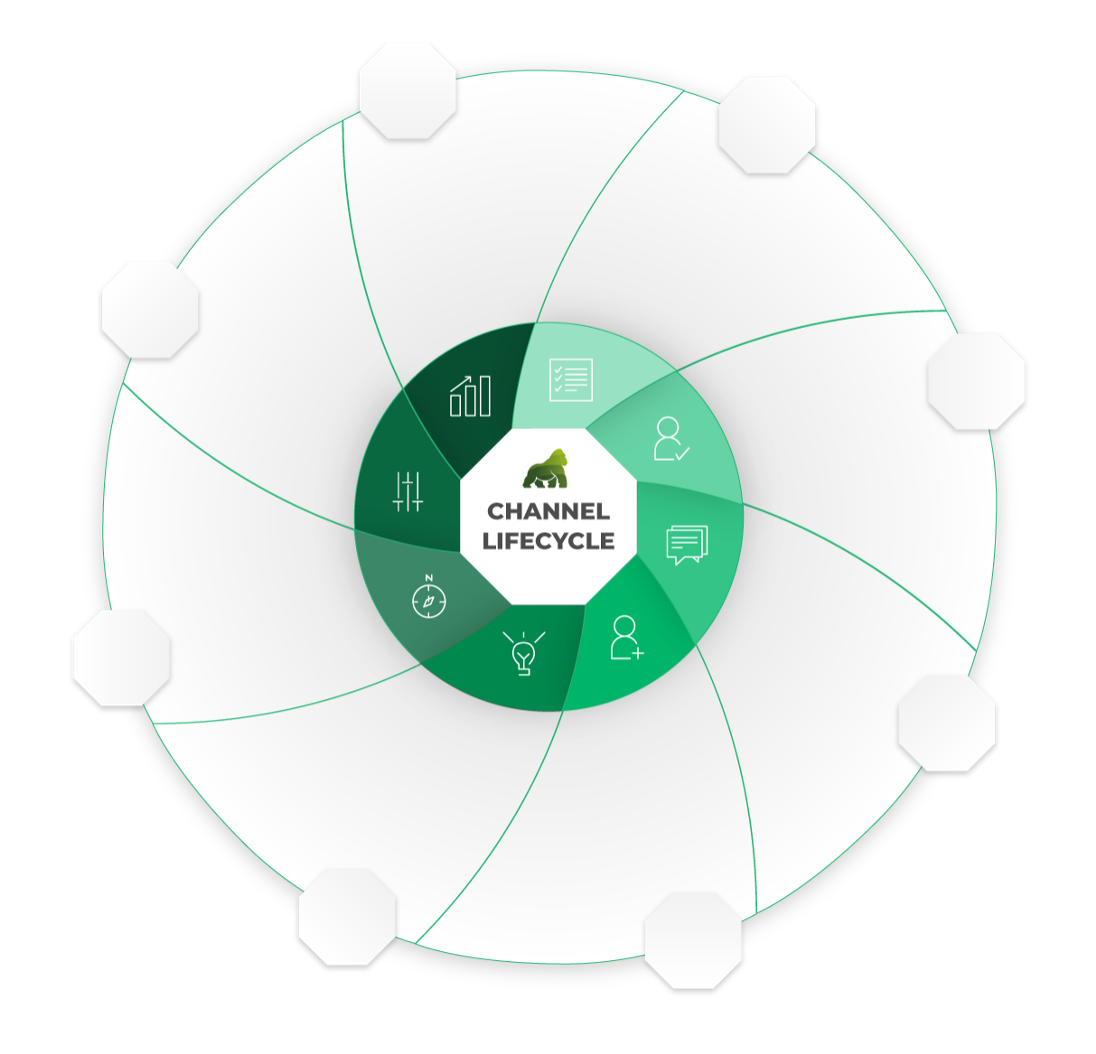 Scaling a technology business through partnership channels and alliances, internationally.
Scaling a technology business through partnership channels and alliances, internationally.
Location: Virtual Fees: 3000
Service Type: Service Offered