

Simon Hartley is an alum of successful startups and Fortune 100 companies, an expert in the business of cybersecurity, mobility, and quantum in hardening critical infrastructure (defense, transport, telco, energy, finance etc.). He joined IBM in 2024 to drive safety, security, and reliability in the US connected vehicles practice. He is also a startup advisor, published author, and public speaker.
- Experienced in startup and Fortune 100 enterprise software management, sales, and marketing
- Skilled at scaling emerging technology, products, and IP in early and highly regulated markets
- Top 25 thought leader and influencer in the business of cybersecurity, mobility, and quantum
Available For: Advising, Consulting, Speaking
Travels From: Washington DC
Speaking Topics: Cybersecurity, Mobility, Quantum
| Simon Hartley | Points |
|---|---|
| Academic | 20 |
| Author | 156 |
| Influencer | 35 |
| Speaker | 21 |
| Entrepreneur | 0 |
| Total | 232 |
Points based upon Thinkers360 patent-pending algorithm.
 Master of Science in Law, Cybersecurity
Master of Science in Law, Cybersecurity
Tags: Cybersecurity, Privacy
 Certificate in Principles and Tools for Cybersecurity IT Leaders
Certificate in Principles and Tools for Cybersecurity IT Leaders
Tags: Business Strategy, Cybersecurity
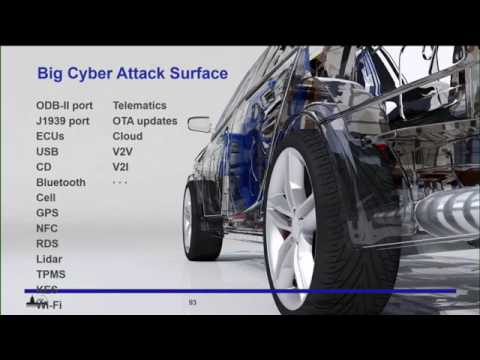
 Automotive is the most disrupted industry
Automotive is the most disrupted industry
Tags: Autonomous Vehicles, Customer Experience, Emerging Technology
 Revving automotive cybersecurity
Revving automotive cybersecurity
Tags: Autonomous Vehicles, Cybersecurity, Mobility
 Gen-x, the Vic-20-and-hi-tech-immigration
Gen-x, the Vic-20-and-hi-tech-immigration
Tags: Emerging Technology, Entrepreneurship, Startups
 Dealing with the Y2K problem
Dealing with the Y2K problem
Tags: Cybersecurity, IT Strategy, Quantum Computing
 Random Number Generation - Who Cares?
Random Number Generation - Who Cares?
Tags: Cybersecurity, Privacy, Quantum Computing
 Tip of iceberg in cybersecurity
Tip of iceberg in cybersecurity
Tags: Cybersecurity, Emerging Technology, Entrepreneurship
 Past illuminates quantum R&D today
Past illuminates quantum R&D today
Tags: Emerging Technology, Quantum Computing
 Rolling the dice - why hardening keys matters!
Rolling the dice - why hardening keys matters!
Tags: Cybersecurity, Privacy, Quantum Computing, National Security
 Making sandals rather than paving the landscape for secure mobile and ZeroTrust
Making sandals rather than paving the landscape for secure mobile and ZeroTrust
Tags: Cybersecurity, Mobility, Privacy
 Power moves in mobile ad tracking
Power moves in mobile ad tracking
Tags: Cybersecurity, Mobility, Privacy
 Now is the time for quantum hardening
Now is the time for quantum hardening
Tags: Cybersecurity, Emerging Technology, Quantum Computing
 Who Controls Your Smartphone and How to Prevent it from Spying on you?
Who Controls Your Smartphone and How to Prevent it from Spying on you?
Tags: Cybersecurity, HealthTech, Mobility
 Is delivering a new security product like delivering a good wine?
Is delivering a new security product like delivering a good wine?
Tags: Business Strategy, Cybersecurity, Design Thinking
 Telework Challenges in a Mobile Device World
Telework Challenges in a Mobile Device World
Tags: Mobility, Future of Work, Business Continuity
 Golidlocks problem of mobile device security in organizations
Golidlocks problem of mobile device security in organizations
Tags: Cybersecurity, Mobility
 Securing Mobile Devices
Securing Mobile Devices
Tags: Cybersecurity, Mobility, Supply Chain
 Smartphones, execs, & travel overseas
Smartphones, execs, & travel overseas
Tags: Cybersecurity, Risk Management, Travel
Tags: Cybersecurity, Emerging Technology, Autonomous Vehicles
Tags: Autonomous Vehicles, Cybersecurity, FinTech
 Data centers must look past perimeter security
Data centers must look past perimeter security
Tags: Cloud, Cybersecurity, Emerging Technology, Data Center
 Want to stop cyber attacks? Why are all of your executables the same?
Want to stop cyber attacks? Why are all of your executables the same?
Tags: Cybersecurity
 Supply chain cyberattacks surging -- How can we prevent them?
Supply chain cyberattacks surging -- How can we prevent them?
Tags: Cybersecurity, Security, National Security
Tags: Cybersecurity, Autonomous Vehicles, Smart Cities
 Top 5 tips to mitigate phone and IoT device hacking in government and enterprise
Top 5 tips to mitigate phone and IoT device hacking in government and enterprise
Tags: Cybersecurity, IoT, Data Center
 Securing the Data Center on Wheels
Securing the Data Center on Wheels
Tags: Cybersecurity, Autonomous Vehicles, Data Center
 SAE Cybersecurity for Entrepreneurs
SAE Cybersecurity for Entrepreneurs
Tags: Cybersecurity, Entrepreneurship, Startups
 Cybersecurity for commercial vehicles
Cybersecurity for commercial vehicles
Tags: Autonomous Vehicles, Cybersecurity, Emerging Technology
 Automated Driving Systems Conference
Automated Driving Systems Conference
Tags: Autonomous Vehicles, Cybersecurity, Privacy
 Consumer Electronics Show (CES)
Consumer Electronics Show (CES)
Tags: Autonomous Vehicles, Cybersecurity, Privacy
 IoT Cybersecurity - An End-to-End Business
IoT Cybersecurity - An End-to-End Business
Tags: Autonomous Vehicles, Cybersecurity, IoT
Tags: Autonomous Vehicles, Cybersecurity, Privacy

Tags: Cybersecurity, Legal and IP, Privacy

Tags: Cybersecurity, GovTech, Mobility

Tags: Cybersecurity, GovTech, Mobility

Tags: Cybersecurity, GovTech, Mobility

Tags: Cybersecurity, GovTech, Quantum Computing
 Bastille and CIS Mobile: Enabling the Safe Use of Employees Cell phones in Secure Facilities
Bastille and CIS Mobile: Enabling the Safe Use of Employees Cell phones in Secure Facilities
Tags: Cybersecurity, Mobility, GovTech
 Quantum Technologies
Quantum Technologies
Location: Washington DC Fees: 0
Service Type: Service Offered
 Billington Cybersecurity Summit
Billington Cybersecurity Summit
Location: Washington Convention Center Date : September 07, 2022 - September 09, 2022 Organizer: Billington