Jul01
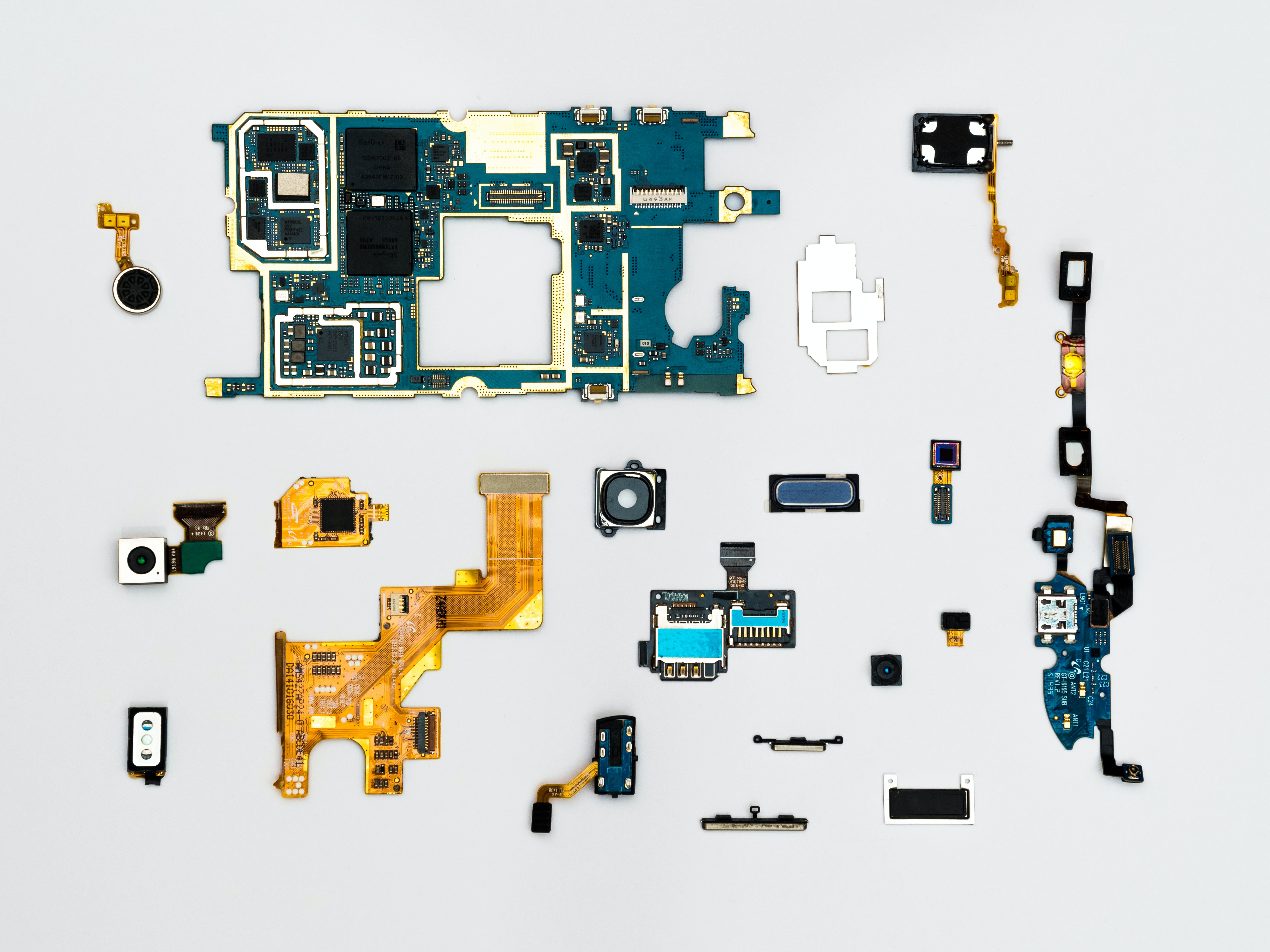
Many large organisations struggle with cyber security toolkit proliferation problems. Surveys after surveys have been placing between 20 and 30 the number of security tools in use in large firms, with all associated problems in terms of visibility, harmonisation and efficiency when it comes to incident handling.
We have asked Corix Partners founder and global cyber security influencer JC Gaillard to give us his views on this matter, which he has been following closely for a number of years.
For the past two decades, most large organizations have kept addressing cyber security as a purely technical problem.
And let’s face it: Many are failing to protect themselves, not just because the threats morph constantly and faster than they can adapt, but primarily because of endemic execution problems around the deployment of technical solutions, and the disconnect between – primarily short-termist – business cycles, and the longer timeframes required to develop cyber security maturity levels in large firms.
In short, cyber security strategies are invariably architected around technical projects and technical tools; but deployment rarely goes beyond alleged quick-wins because business priorities shift constantly, and rarely look over the mid to long-term – as would be required in many firms to deliver real and lasting change around cyber security.
CISOs leave after a few years out of frustration over slow progress (and for more money), and the technical debt keeps piling up… all tendencies which have been greatly aggravated by the COVID pandemic…
After two decades of playing that game, some cyber security practices are now operating around up to 20 or 30 different tools in large organizations according to some surveys.
The main problem is that nothing is never joined up because it is simply the result of decades of organic short-termism, “strategic” plans which were never strategic or never rolled out, and knee-jerk reactions in response to incidents or audit observations, or panic buying ahead of regulatory inspections.
It results in complex security operational processes, poorly integrated, excessively manual, repetitive and boring for the analysts in charge of delivering them, and tremendously expensive to scale up.
To scale up if you can find the skills that is…
Because most industry sectors have woken up to the criticality of cyber security following the avalanche of cyber-attacks we have been seeing over the past decade and are now competing for a resource pool which has not grown sufficiently over the period.
People asking themselves why the cyber security resource pool has not grown sufficiently over the years need to look beyond educational and training issues: It is not only the talent acquisition rate which is too low across the cyber security industry, it is also the retention rate, and that is essentially linked to those dysfunctional operational processes and the “boring” entry-level jobs of many analysts, who undoubtedly didn’t get into cyber security to end up cutting and pasting data into Excel sheets or to produce useless reports simply designed to put ticks in compliance boxes. At the first available opportunity, they leave to do something more exciting, and they don’t come back…
At the heart of this, conveniently fuelled by the tech industry, lie the excessive focus on tech products to solve cyber security challenges, the reverse engineering of processes around the capabilities of tools, and the colossal accumulation of technical debt in that space over the past two decades, which is the result of execution failures and lack of priority focus by business leaders.
Senior executives who want to break out of that spiral need to stop buying more tech for the sake of it and start focusing on the decluttering of their cyber security landscape.
“For every one new solution, remove two legacy solutions” suggests Greg Day (VP & CSO, EMEA, Palo Alto Networks) and it sounds like a good start.
But to achieve that, cyber security leaders will have to look back at the structure of their operational processes and streamline those.
They will also have to look differently at automation and focus it on improving analysts efficiency, allowing them to dedicate more time to the challenging tasks for which they have been trained and hired.
Ultimately, cyber security leaders will have to go back where all this should have started: “People, Process then Technology”.
Technology not for technology-sake, but in support of security Processes, which are designed to protect the firm and its People from the cyber threats they face.
It is more difficult to execute and to sell internally than buying the next shiny tool to put a tick in some compliance box but stopping the creation of technical debt and bringing the existing one under control has become vital to the future of the cyber security industry.
Keywords: Cybersecurity, Leadership, GRC
 Friday’s Change Reflection Quote - Leadership of Change - Change Leaders Confront Instability Early
Friday’s Change Reflection Quote - Leadership of Change - Change Leaders Confront Instability Early The Corix Partners Friday Reading List - May 22, 2026
The Corix Partners Friday Reading List - May 22, 2026 Space as the Next Network Edge: The Evolution of Global Connectivity
Space as the Next Network Edge: The Evolution of Global Connectivity The Roaming Coach Model to Solving Leadership Knowledge Deficits
The Roaming Coach Model to Solving Leadership Knowledge Deficits  UPS’s Profitability Pivot Is Fueling a Labor Fight
UPS’s Profitability Pivot Is Fueling a Labor Fight