Nov20

Author’s Note. This post is short. The topic is incredibly important and nuanced and worthy of a much longer article. At this point though I’m keeping this short and snappy to ensure maximum attention.
One might think that with a decade’s warning there’s plenty of time to act. Well, a couple of questions?
Even if the answer to these is ‘not currently’ then one might think with a bit of a push momentum could increase.
That however is thinking only about the future risk. Not the present risk.
Most of the petabytes of data we produce every day is of little value to anyone beyond the creator and his/her intended audience. However, as we well know there is data that can have value to third parties when stolen.
This takes multiple forms: fraud linked to theft of social security or credit card details of individuals; corporate or personal ‘blackmail’ from confidential information; corporate secrets around product design, manufacturing processes; and so many more
Most data has an “expiry date” — the point at which it ceases to have value. The expiry date on any piece of data may vary for different ‘users’ of the data.
Take a credit card number. Once the card is expired it has no obvious use to a criminal as it’s hard to make a purchase with an expired card. For the original owner, they may see value in that number at a later date if for example, they want to claim a refund on a product bought with the card.
Similarly, a young professional may at some point see no further value in photos from hedonistic college parties, while someone trying to discredit the individual in the future may find it worth holding onto those photos for a longer period.
Typically though data, becomes less valuable over time. If that time is a few years then this topic is not relevant. If the data still has value in a decade or two, then someone having access in the future is a genuine (business) problem.
If you think about it, there is plenty of data that will still have value in a decade or more — medical data, banking data, military plans, government decisions, the recipe for Coke…
Data hacks are regularly in the news. In fact it has become so common that they rarely make headlines unless there is some kind of spin — e.g., a huge number of impacted people or particularly juicy data
Those are the ones we hear about. What about those we don’t?
Given most data is encrypted both at rest and in transit stealing it in a usable form requires either a degree of luck (searching for something that accidentally hasn’t been encrypted or where the decryption key is accessible) or careful planning (by inserting yourself at a point where the data is ‘in use’ and (appropriately) not encrypted).
As such many cyber weaknesses are not a major problem as the risk and cost — to the data owner, the responsible organization, the insurer etc — of loss of well-encrypted data is far less than unencrypted data (though reputational damage may still be significant )
Enter quantum computing and HTDT.
If we think back to our opening statements, we know that we are getting close to when people will have access to quantum computers that can decrypt many of the common encryption protocols.
Thus, what if fully-encrypted data was stolen and held onto? As long as the data expiry period is longer than the period before decryption is possible there is value to the thief and damage to the original owner.
Furthermore, when a hack becomes public, changes are made to stop the problem. If data is being stolen and no noise made about it, how long might the security hole remain open allowing a continual siphoning off of that data?
This concept of harvesting data today, and then decrypting in the future is what makes this top one of real urgency. Urgent for information security teams to think about; and urgent for cyber underwriters to consider.
This topic needs broader discussion, and while it may not appear as pressing as post-pandemic recovery, and rebooting the drive around sustainability, it is deserving of a place in your “key topics for 2021” discussion list.
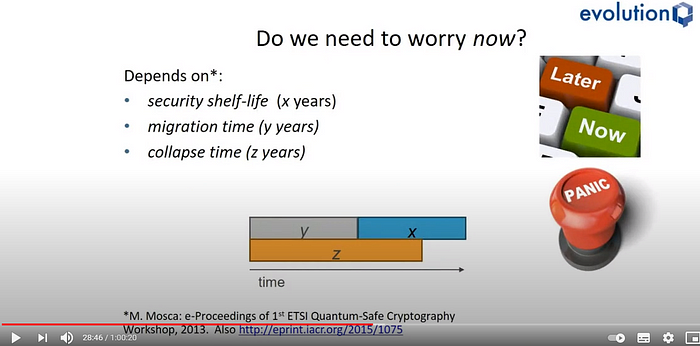
Image from presentation by Prof Michele Mosca to Quantum London (see video here) showing why we need to start thinking now0
The millennium bug
Some commentators draw parallels to the so-called Millennium Bug. As you may recall, this was the fear that as the two-digital year counters in older IT systems moved from 99 to 00 at midnight on 31 December 1999, computers would get confused with unpredictable and potentially devastating results.
As it turned out we all awoke on the morning of 1/1/2000 and the world was still there. Many decried the vast amounts of money spent on the problem; others pointed out that it was fine as a result of that spend!
The lack of just about any major failure back at the turn of the millennium will likely hamper communication on this risk with plenty of executives suggesting it is fear-mongering on the part of risk managers or CISOs who are looking for additional budget.
Time will tell how things play out.
By Paolo Cuomo
Keywords: Cybersecurity, Quantum Computing, Risk Management
 Designing Coherent Systems
Designing Coherent Systems 9 cose che ho imparato nella culla dell’intelligenza artificiale
9 cose che ho imparato nella culla dell’intelligenza artificiale The Corix Partners Friday Reading List - June 5, 2026
The Corix Partners Friday Reading List - June 5, 2026 Friday’s Change Reflection Quote - Leadership of Change - Change Leaders Enable Institutional Capability
Friday’s Change Reflection Quote - Leadership of Change - Change Leaders Enable Institutional Capability The Difference Between Executive Success and CEO Readiness
The Difference Between Executive Success and CEO Readiness