 https://medium.com/@vamsi-mohan/revolutionizing-quantum-computing-with-web-services-ee77860123f9
https://medium.com/@vamsi-mohan/revolutionizing-quantum-computing-with-web-services-ee77860123f9
Medium
February 28, 2023
Quantum computing is a costly affair. How do we leverage the benefits of advanced computing power? There is a solution for obtaining results via web services and serving them to end users. Quantum computing and web services can be combined to create powerful applications that can solve complex problems that are beyond the reach of classical computing.
Quantum computing and Web services are two different technologies that can be used together to enhance the performance and capabilities of web applications.
See publication
Tags: Quantum Computing
Revolutionizing Telecommunications: The Role of Quantum Computing in the Future of Communication
Medium
February 19, 2023
More than a quarter of my engineering experience went into working with the telecommunications domain and serving Fortune 100 telecom OEMs, and telco network service providers.
Digitalization is becoming critical and imperative in order to thrive in the market. Especially in the telecommunications industry, it is more evident. We just started using 5G and talking about 6G. Some well-known corporations are talking about Quantum Internet and QCaaS (quantum computing as a service) to better serve their customers.
See publication
Tags: Quantum Computing, Telecom, 5G
 Advancing Quantum Computing through Industry-Academia Collaboration
Advancing Quantum Computing through Industry-Academia Collaboration
Medium
February 15, 2023
Quantum computers hold great promise for solving problems that are currently intractable for classical computers, but the field is still in its early stages. While many impressive experimental results have been achieved in recent years, quantum computers are not yet ready for production use in most applications.
Industry-academia collaboration is crucial for advancing quantum computing research and development. Quantum computing is a complex and multidisciplinary field that requires the expertise of scientists and engineers from academia, industry, and government. Collaboration between these sectors can accelerate the pace of innovation, facilitate the transfer of knowledge and technology, and provide opportunities for education and workforce development.
See publication
Tags: Quantum Computing, Education
 Hybrid Quantum Computing: Are You Prepared for the Next Technological Shift?
Hybrid Quantum Computing: Are You Prepared for the Next Technological Shift?
Medium
February 10, 2023
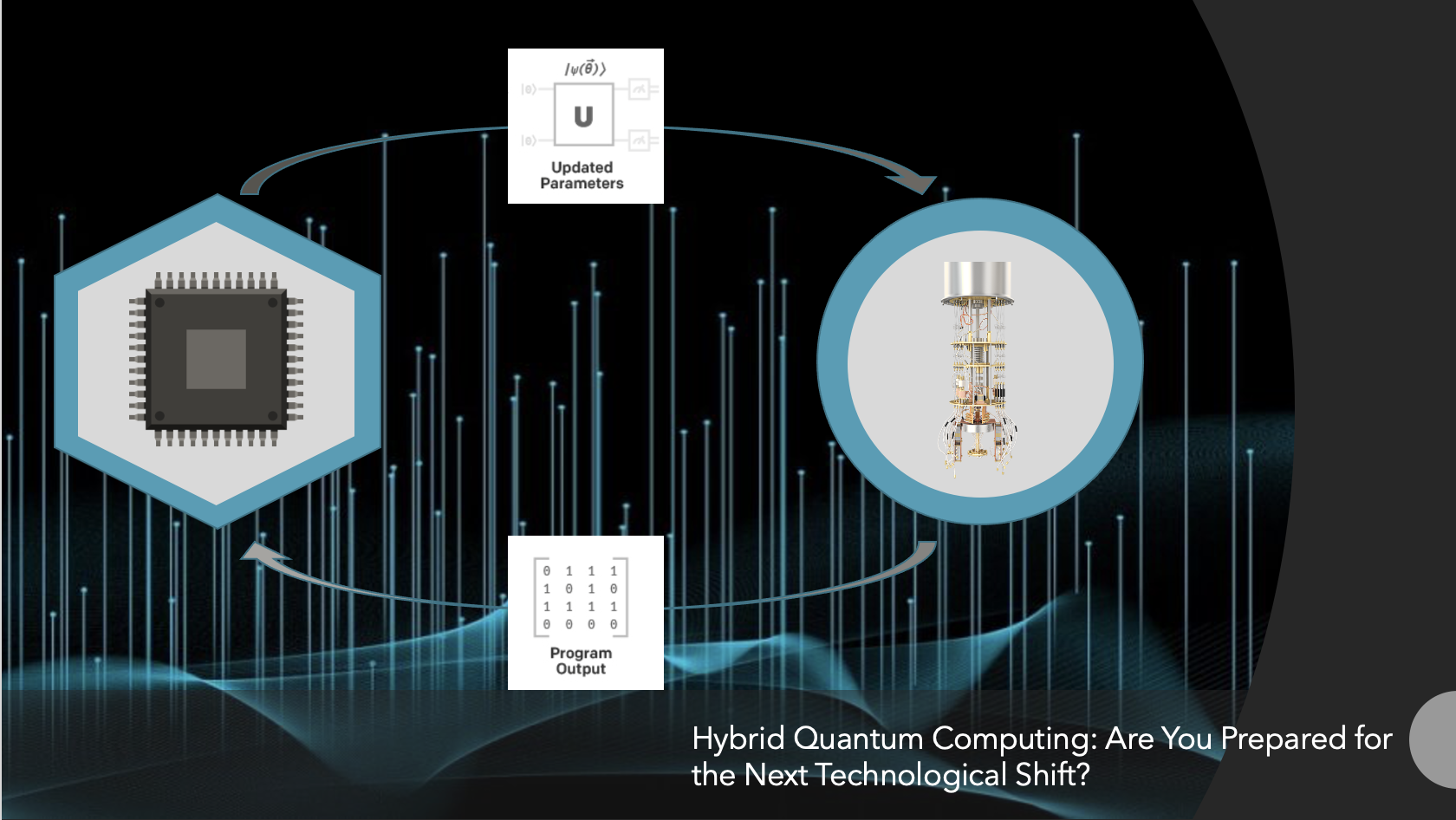
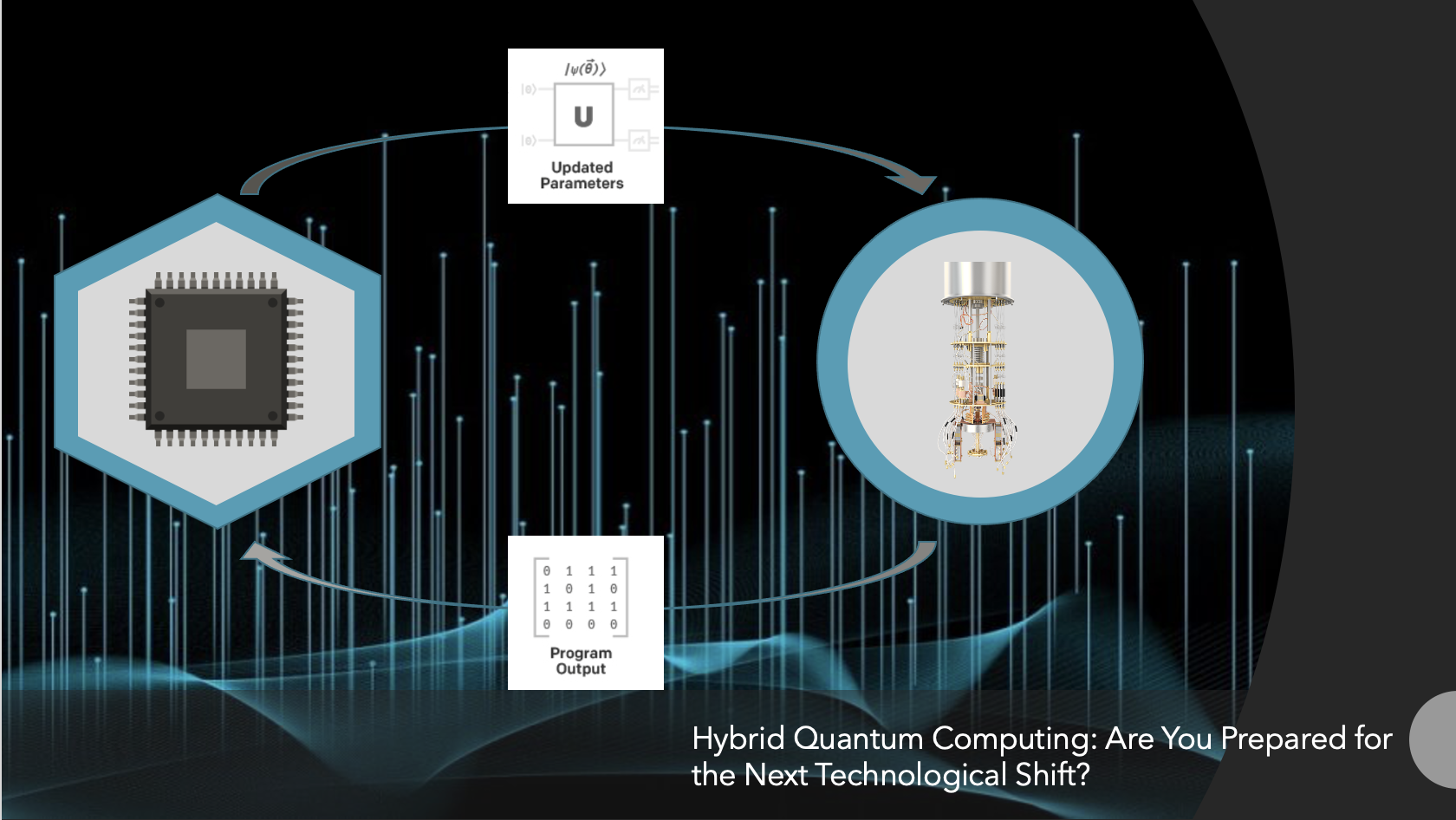
In the past decade, quantum hardware has achieved dramatic improvements in gate fidelities, qubit coherences, and qubit counts. Small quantum circuit fragments have been experimentally realized with superconducting qubits as well as with ion traps. However, due to fundamental limitations in the engineering, the number of qubits on a chip, gate fidelities, and qubit coherence times will remain modest in the near future.
In addition to that, we are all aware that setting up a quantum computing environment is costly and time-consuming. It has taken years and decades to advance Google's Sycamore system from 53 qubits to the thousands of qubits needed to perform large-scale computations. Then, what is the alternative to reaping the benefits of quantum power?
See publication
Tags: Quantum Computing
 New Methods for Estimating Quantum Computing Requirements
New Methods for Estimating Quantum Computing Requirements
Medium
February 01, 2023
Quantum computing and its real-time application implementations are rapidly growing. We can expect many enterprises to use quantum computing applications in the near future. The QSPs (Quantum Service Providers) like IBM, Google, Rigetti, AWS, and Azure are already planning to offer services in the hybrid quantum computing space.
In November '2022, IBM unveiled its largest quantum processor, which knits together a mere 433 qubits. IBM is aiming to scale up its systems to more than 4,000 qubits by 2025, and D-Wave Systems is planning to roll out a 7,000-qubit annealing quantum computer in the 2023–2024 time frame.
If the technology and offerings are rapidly advancing, we'll be deploying our real-time application in production very soon. However, there is a problem: how can the quantum computing sizing and estimations be solved?
See publication
Tags: Quantum Computing
 Fostering the human–machine alliance
Fostering the human–machine alliance
Medium
January 20, 2023
Rather than fearing the rise of machines, automation, enterprises would embrace them to reap the benefits for the betterment of the ecosystem.
Global inflation is rising, and the economy's and labour costs' volatility has impacted turnover. Top executives make cost management and efficiency their top priorities. Automation offers enterprises a way to make progress across their production lines.
Global executives should revisit their operating models and processes to reap the benefits. Machines can do more than simply make parts. They can be trained and used intelligently. The human workforce believes machines are coming to grab their jobs. It was the same scenario in the early 1990s, when computers were first made available to the general public. However, we have seen the benefit, and it has become part of our lives. In fact, revenue growth increased significantly after computerization in multiple disciplines. This was the result of digitization, digitalization, and digital transformation.
See publication
Tags: Quantum Computing, Ecosystems
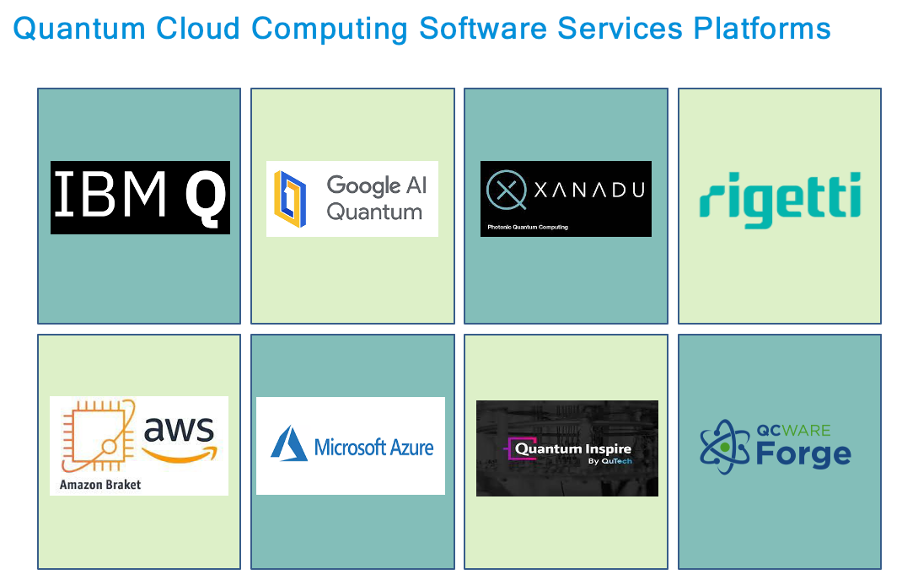
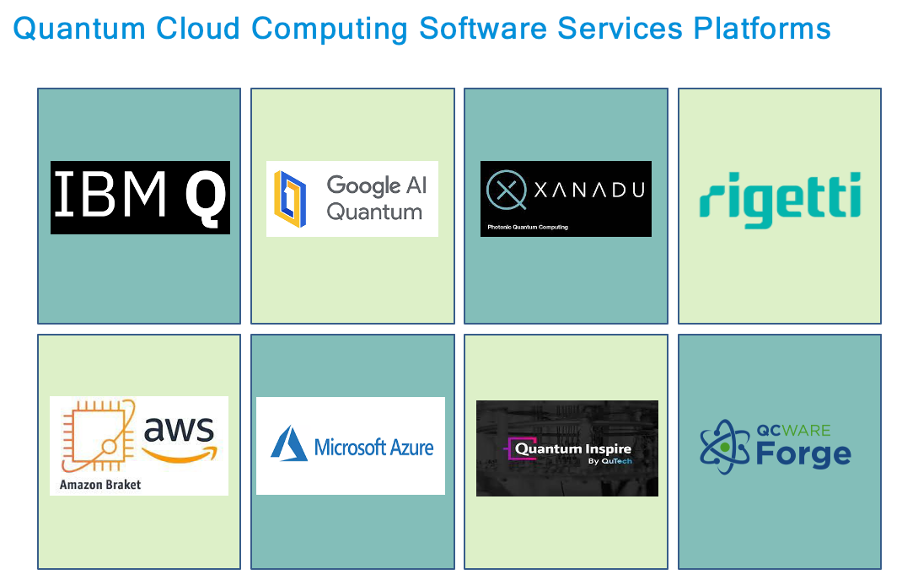 Quantum Cloud Computing Platforms
Quantum Cloud Computing Platforms
Medium
January 12, 2023
Quantum computing infrastructure refers to the hardware and software systems that are used to build and run quantum computers. This includes the physical devices that make up the quantum computer, such as qubits (the basic units of quantum information) and the devices used to control and manipulate them, as well as the software and algorithms that are used to program and run quantum computations. Building and maintaining a quantum computing infrastructure can be challenging due to the complexity and fragility of the systems, and the need for specialized expertise in both physics and computer science.
The history of quantum computing infrastructure can be traced back to the early days of quantum mechanics in the 1920s and 1930s. The basic principles of quantum computing were first proposed in the 1980s by Paul Benioff and Yuri Manin, but it wasn't until the 1990s that the first functioning quantum computers were built. Early quantum computing experiments were primarily focused on demonstrating the principles of quantum computing, rather than on building useful computational devices.
See publication
Tags: Quantum Computing, Cloud, Cloud
 Software modernization to embrace quantum technology
Software modernization to embrace quantum technology
Medium
January 08, 2023
Software modernization is a continuous activity when technology changes. To leverage the benefits of new technology and frameworks, software modernization is required. It is the process of updating or replacing outdated or legacy software systems to meet current and future business needs. There are many reasons why enterprises might choose to modernize their software, including the desire to improve efficiency, reduce costs, or take advantage of new technology such as quantum computing.
See publication
Tags: Quantum Computing
 Interpolation for Datasets
Interpolation for Datasets
Medium
August 05, 2022
nterpolation is a statistical technique that estimates an unknown price or possible yield of an asset using related known variables. The unknown values can be interpolated by using other known values that are in the same order.
Interpolation is a method of estimating a function’s value for any intermediate value of the independent variable, whereas extrapolation is the process of calculating the function’s value outside of the specified range.
See publication
Tags: Big Data, Emerging Technology, Predictive Analytics
 A future reality - Hackers attacking human memories
A future reality - Hackers attacking human memories
LinkedIn
July 05, 2021
Neurostimulators may be a boon for patients who are suffering from Parkinson's disease or people suffering from deep depression. The Black Mirror series may sound like science fiction, it is worth realizing that we are already on the way to understand how human memories are created, processed, and restored. Many experiments in the recent past shown the possibilities of improving human memories (especially short-term memories).
See publication
Tags: AI, Cybersecurity, Health and Safety
 AI is the future strategy of Enterprises
AI is the future strategy of Enterprises
LinkedIn
February 06, 2021
Artificial Intelligence is optimizing the way of doing business. It is helping enterprises in enabling predictions with supreme accuracy, automating business processes, and complex decision making.
See publication
Tags: AI, Autonomous Vehicles, Business Strategy
THE NEW WAYS OF EMPLOYEE UPSKILLING DURING COVID-19 LOCK DOWN
ANECDC
May 17, 2020
The corporate culture is getting changed during and post COVID-19 lockdown. Most of the employees are asked to work from home except essential workers and employers are reviewing their risk mitigation strategies and planning to sustain their revenues. The practice of engaging employees is getting changed due to remote working culture.
See publication
Tags: EdTech, Leadership, Social
Robotic Process Automation - Solid steps to cognitive revolution
LinkedIn
April 24, 2019
It is evident, many enterprises are started using software robots to perform business processes by spying the ways in which people perform their routine jobs. Robotic process automation (RPA) is an emerging trend rapidly growing in the digital market. In today's world, the biggest adopters of RPA include banks, insurance companies, utilities and telecommunications companies. Many enterprises and financial intuitions are started using RPA together with intelligent cognitive technologies/frameworks like Chabot, speech recognition, and machine learning to automate the tasks. RPA tools mimic the “routine manual” tasks performed by the human workers. The market provides a broad range of solutions with tools either operating on individual desktops or enterprise servers or from the cloud. Leveraging the capabilities of cognitive with RPA can help enterprises to become more efficient and agile in the process of digitization.
See publication
Tags: Digital Transformation, Digital Disruption, RPA
Your obsessive smartphone habits just became the Cambridge Dictionary’s word ("Nomophobia") of the year
LinkedIn
December 03, 2018
Communication helped us to improve many things in the fast paced world. People are able to communicate with others who are thousand miles away from them. Smartphones often serve as a go-to source for many and the addictive behaviour to smart phones are also increased.
The Cambridge English Dictionary added a new word "nomophobia" (or, no-mobile-phone-phobia). Due to excessive technology or I might be wrong... due to excessive using of smart phones, the distraction level of a normal human being is increased. The more technology the more distraction. Ultimately blaming the technology that it is not allowing us to concentrate. Is it right?
See publication
Tags: Culture, Digital Transformation, Health and Safety
The Data Center Is Dead, and EDGE Infrastructures Emerge
LinkedIn
November 23, 2018
Traditional Data Centers are getting dead due to Cloud revolution. Enterprises believe deploying data in Cloud is the best way to store and process. However, new methods and techniques are changing the trends. We have observed in the last decade, computing workloads have been migrating from traditional hosting at on-premise data centers to cloud. According to Cisco, the cloud traffic is likely to rise nearly fourfold by 2020, increasing to 14.1 ZB per year by 2020.
See publication
Tags: Cloud, Data Center, Digital Transformation
Serverless Technologies -The Future of Business Computing
LinkedIn
August 26, 2017
Initially, the definition of serverless architecture was limited to applications which are dependent on third-party services in the cloud. The rise of Machine learning, Mobile and IoT applications is fueling the growth of serverless computing platforms. It is a cloud computing execution model in which the cloud provider dynamically manages the allocation of machine resources. Pricing is based on the actual amount of resources consumed by an application, rather than on pre-purchased units of capacity. However, what is not clear is whether this reduction of resource usage and operational efforts are valid and whether these reductions are consistent across all serverless computing platforms.
See publication
Tags: Cloud, Data Center, Innovation
The Leadership Way : Building Trust in the Workplace
LinkedIn
August 15, 2016
When I think about all of the different dynamics that combine to create a successful workplace, one of the most important factors, in my mind, is trust. In a trusting environment, we’re empowered to make decisions and encouraged to take risks.
Leadership experts will always agree on one thing: to be a successful leader you must be a trustworthy leader. And in today's uncertain corporate world, it is not surprising that study after study shows a decline in the employee trust on their leaders. If your employees don't trust your organization leaders, they cannot truly lead them. Employees will doubt every word their leaders say, and leaders will have no credibility to influence. According to the leadership surveys, one in four employees doesn't trust their Leaders.
See publication
Tags: Culture, Leadership, Social
Attitude Problems in the Workplace: How to deal employees shift from a victim mindset?
LinkedIn
June 30, 2016
In the Corporate World, "attitude" is a bit of a buzzword. One's mental attitude, whether positive or negative, healthy or unhealthy, is said to be a key factor in the success of organizations and professional relationships.
People are the pillars for maintaining the right culture to grow organizations. Organizations often feel trapped when dealing with attitudes of entitlement among their staff members. Leaders have to nurture the skills to manage and control workplace attitude problems. It is becoming a bad symptom having attitude problems in the Workplace. People are spending an average eight hours a day, five days a week for about 45 weeks a year. That is a long time, and it essentially means that people are spending probably the majority of their lives at work.
See publication
Tags: Culture, Leadership, Social
The Leadership Nature
LinkedIn
May 14, 2016
According to Harward Business Review, Considering the challenges of the 21st century enterprise: things change too fast for one individual to know how best to respond; there are hundreds of explanations for any small event, and multiple perspectives are needed to understand what that event means and decide what to do; a pipeline of future leaders is essential to companies’ long term success.
When it comes to leadership, talk really is cheap. The best leaders don’t lead from position or authority. Leadership is in Action and Not in Talk. Many leaders talk about many things. They quote many examples and give hours of speech on leadership behavior and qualities. But when it comes to their own, the things play differently. Leadership should be in their Action. People do not want to hear the words; they want to see results. Politicians are the best example of this topic. They provide excellent material in the form of words and serve as a perfect sample of how some “leaders” spend too much time talking (way too much, actually) and not enough time doing. It is the same even in Corporates. By seeing their actions, people are losing faith on their leadership teams. It is witnessed in many exit interviews. It is a dangerous situation for the Corporates.
"Never tell people how to do things. Tell them what to do and they will surprise you with their ingenuity" —General George Patton
See publication
Tags: Culture, HR, Leadership
Are Exit Interviews a Waste of Time?
LinkedIn
May 04, 2016
Nothing good comes from an exit interview.
Most of the employees think "Nothing good comes from an exit interview. You won't learn anything you don't already know and no one wins in the process. That's pretty declarative". But is it true? Who created that impression?
"Exit interviews offer the opportunity for the employer to clear up misunderstandings and demonstrate concern for the employee's point of view."
The exit interview with a resigned employee is the best opportunity to obtain information about what the organization is doing well - and, what the organization needs to do to improve. Exit interviews are a rich source of information for organization's improvement.
See publication
Tags: Culture, HR, Leadership
Cyber Security Challenges in the Digital World
LinkedIn
April 28, 2016
In the growing digital world, Cyberattacks have become an everyday threat. They not only affect financial and customer data, but machinery and industrial engineering companies through networked production systems and software-laden products. A holistic approach is needed to fully counter these threats.
Recently hackers attack on Intelligence Agency, data theft from US government agencies, a spy attack on the German federal government. A recent American Bar Association survey found that one in four law firms with at least 100 attorneys have experienced a breach. Leading New York Law Firms hacked by Cyber attackers. Four North American hospitals The Ottawa Hospital, Kentucky Methodist Hospital, Chino Valley Medical Center and Desert Valley Hospital were recently infected with ransomware in March 2016: Spectacular cases of cybercrime like these are now a regular feature of daily news headlines. Indeed, cyber security attacks have become a major threat to companies around the globe and across all industries. From the year 2010, annual cyberattacks globally have increased ten times over.
See publication
Tags: Cybersecurity, Digital Transformation, Emerging Technology
Neutralizing the Negative Workplace Environment
LinkedIn
April 25, 2016
Every organization wants zero attrition and hundred percent success. However growing organizations frequently experience issues with negative workplace environment. Even it is common for the organizations which are top 5 in "Great Place to Work" award winners.
Happy employees, workplaces create successful organizations. Negative employee attitudes and less-than-professional behavior can poison the workplace environment. Employee morale describes the overall outlook, attitude, satisfaction, and confidence that employees feel at work. When employees are positive about their work environment and believe that they can meet their most important career and vocational needs at work, employee morale is positive or high.
See publication
Tags: Culture, HR, Leadership
Building A Winning Culture
LinkedIn
April 09, 2016
What holds an organization together and motivates the people within it to do the right things rather than the easy things? The answer, for many top-performing companies, i.e. A Winning Culture. In recent Bain survey, 81% of executives agreed that a company without a winning culture was “doomed to mediocrity”.
The organizations are often in a situation how to develop successful teams and reap the benefits of high performing culture. The research is shown that high performance culture shown increase of profitability sometimes as high as 700% or even more. A company’s culture can have a powerful impact on its performance. Culture is an interface that binds an organization together to form the successful teams.
See publication
Tags: Culture, HR, Leadership
Secure Data Transmission through IBE and Symmetric Encryption Techniques
International Conference on Smart Technology in Computer Science and Information Technology (CSIT-2019)
November 20, 2019
There are many techniques, methods and methodologies in secure data transmission. However, still users are failing to transmit the data securely. Hackers are succeeding in attacking the data for every few minutes. In cyber security attacks, SQL Injection and Cross Site Scripting attacks are very prominent. SQL Injection (SQLI) executes malicious code in the form of SQL statement at database by directly executing the query or changing the requested parameters, changing the triggered URL. In case of Cross-Site Scripting, the attacker targets to execute the malicious code at the client side. In this paper, for secure data transmission, we proposed a model using IBE and AES encryption techniques. we explained the proposed model "How to transmit the data securely?".
See publication
Tags: Cybersecurity
User Centric Security Models for Improving the Data Security from SQL Injections and Cross Site Scripting Attacks
International Conference on Internet of Things, Big Data Analytics and Information Technology (ICITBDIT– 19)
October 20, 2019
SQL Injection Attacks (SQLIA) and Cross-site Scripting Attacks (XSSA) are frequently used by hackers to hack the user data. SQL Injection (SQLI) executes malicious code in the form of SQL statement at database by directly executing the query or changing the requested parameters, changing the triggered URL. In case of Cross-Site Scripting, the attacker targets to execute the malicious code at the client side.
See publication
Tags: Cybersecurity
Security Framework for Detecting the SQL Injection and Cross Site Scripting Vulnerabilities
7th International Conference on Research Developments in Applied Science, Engineering & Management
June 20, 2019
From the last two decades, SQL Injection Attacks (SQLIA) and Cross-site Scripting Attacks (XSSA) became prominent of taint-based vulnerabilities which has caused many security breaches in the digital industry. SQL Injection (SQLI) executes malicious code in the form of SQL statement at database end whereas in the case of Cross-site scripting, the attacker targets to execute the malicious code at the web browser (client) side. In this paper, we are trying to propose a security framework to detect SQLI and XSS attacks. Regression Neural Network (RNN) introduced to identify and control the dynamic systems.
See publication
Tags: Cybersecurity
A Detection Framework for SQL Injections and Cross Site Scripting
International Journal of Science & Engineering Development Research (IJSDR)
January 15, 2019
Designing secure web applications are most important aspect to avoid SQL injections and Cross Site Scripting (XSS) attacks. XSS vulnerabilities are classified into three types. i.e., Reflected XSS, Stored XSS and Dynamic XSS. From these types of XSS, DOM XSS is different from the two others. There are many researches and detection methods proposed for Reflected XSS and Stored XSS. However, it is not suitable for Dynamic XSS. Due to increase of web applications, the threats are getting increased. XSS often included in OWASP top-10 list from the last decade and hence an appropriate XSS detection method is necessary. In this paper, we propose a detection framework for SQLI and XSS. We introduced Regression Neural Network (RNN). It provides accurate and quick solution to regression, approximation, classification and fitting problems. RNN can be used in system identification of dynamic systems as well as control of dynamic systems. Here we are integrating multi-objective optimization which involves integration of objective formulation from dragon fly optimization (DA) and Genetic algorithm (G A). Integrating of optimization algorithm, crossover and mutation is used instead of alignment process of DA.
See publication
Tags: Cybersecurity
User Centric Security Models for Improving the Data Security from SQL Injections and Cross Site Scripting Attacks
Journal of The Gujarat Research Society
October 20, 2019
SQL Injection Attacks (SQLIA) and Cross-site Scripting Attacks (XSSA) are frequently used by hackers to hack the user data. SQL Injection (SQLI) executes malicious code in the form of SQL statement at database by directly executing the query or changing the requested parameters, changing the triggered URL. In case of Cross-Site Scripting, the attacker targets to execute the malicious code at the client side.
See publication
Tags: Cybersecurity
Security Framework for Detecting the SQL Injection and Cross Site Scripting Vulnerabilities
International Journal of Scientific Research and Review
June 20, 2019
From the last two decades, SQL Injection Attacks (SQLIA) and Cross-site Scripting Attacks (XSSA) became prominent of taint-based vulnerabilities which has caused many security breaches in the digital industry. SQL Injection (SQLI) executes malicious code in the form of SQL statement at database end whereas in the case of Cross-site scripting, the attacker targets to execute the malicious code at the web browser (client) side. In this paper, we are trying to propose a security framework to detect SQLI and XSS attacks. Regression Neural Network (RNN) introduced to identify and control the dynamic systems.
See publication
Tags: Cybersecurity
Proposed Adaptive Algorithms to Prevent SQL Injections
International Journal of Advance Engineering and Research Development
December 22, 2017
For the last two decades, SQL injection attacks are considered as common for Web applications. By growing of digitalization, the security attacks are increasing and most commonly SQL Injection Attacks (SQLIAs). Injection attacks considered in the first place (A1) as per the OWASP Top 10 Application Security Risks for the year 2017. To overcome these attacks, many researchers and scientists proposed various algorithms to adopt. However, software industry has not completely succeeded from the SQL injection attacks and vulnerabilities. In this paper, we examined various algorithms proposed by different researchers to prevent the SQL injections.
See publication
Tags: Cybersecurity
Secure Web Applications Against Cross Site Scripting (XSS): A Review
International Journal of Trend in Scientific and Development (IJTSRD)
November 30, 2017
Cross Site Scripting (XSS) attacks are most common vulnerability issues in the digital era for the Web applications. These attacks occur, when an attacker uses a web application to send malicious code in the form of client side script. These scripts exploit the vulnerabilities in the code and resulting in a serious consequence like theft of cookies, passwords and any confidential user data. In extreme cases, the user may have lost his/her control on the browser. In this paper, we explained detection, and prevention of Cross Site Scripting (XSS) vulnerability attacks through a systematic review process.
See publication
Tags: Cybersecurity
Detection and Prevention of SQL Injection Vulnerabilities in Web Applications: A Review
International Advanced Research Journal in Science, Engineering and Technology
September 25, 2017
In recent time, web security has been viewed in the context of securing the web application layer from attacks by unauthorized users. The vulnerabilities existing in the web applications are targeted through SQL Injection attacks (SQLIA). In this paper, we explained various method of detection and preventive measures on SQL Injection Attacks through a systematic review process.
See publication
Tags: Cybersecurity
Debunking of common attacks in web applications
International Journal of Current Research
March 28, 2017
Cyber-attacks are becoming commonplace in our society these days as the world becomes more connected. Security attacks on information security infrastructure have continued to evolve steadily and legacy network based attacks have been replaced by more sophisticated web application based attacks. It is vitally important to discuss web application attacks considering the number of attacks happened in the recent years. In this paper, we define each of them in detail and emphasize their differences. We also conclude our studies in this area with providing a diagram which gives a comprehensive overview about Web attacks.
See publication
Tags: Climate Change
The Intensity of Fault Slip through in Software Process
International Journal of Scientific and Engineering Research (IJSER)
March 18, 2012
The improvement of software development process is gradually refining. Software companies are trying to deliver bug-free, efficient product in a less time. Now a days, the competition between the IT companies are increased and the companies need improvements that can decrease the lead-time and improve the delivery precision. It is not enough, if companies develop the products on time but also need to be considering the quality of the product. Efficient and effective testing methods find bugs in early stages rather than finding in later stages or in production time. Early catching of bugs will reduce the rework time and also cheaper to find and remove. Rework commonly accounts more than half of the development time. The main reason for high rework cost is because of fault slippage from earlier phases. As an input to this improvement, this article explains the intensity of fault-slippage, which determines the faults that could have been more cost efficient to find in earlier phases of software development and life-cycle.
See publication
Tags: Change Management, Digital Transformation
 6th World Test Engineering Summit - Thought Leadership Honor
6th World Test Engineering Summit - Thought Leadership Honor
1.21GWS
December 15, 2022
Conference Schedule (15 December, 2022)
Theme : Quality Assurance & Microservices, Containers and Serverless
See publication
Tags: Digital Transformation
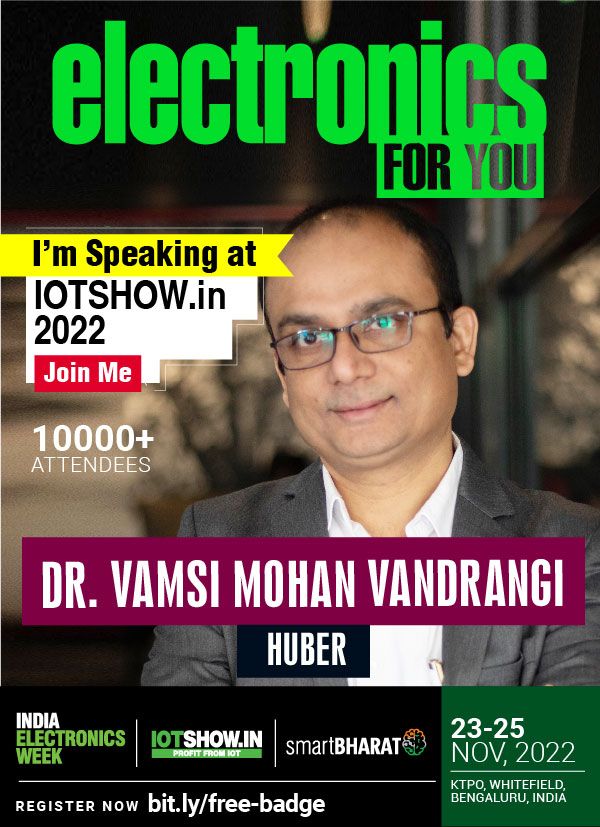 SECURING YOUR IOT APPLICATIONS WITH DEVOPS
SECURING YOUR IOT APPLICATIONS WITH DEVOPS
India Electronics Week (IOTShow.in)
November 25, 2022
DevOps, with its focus on reducing delivery cycle times, can increase the speed of IoT systems development that can be integrated in a seamless and secure manner. Seamless integration can be achieved through a combination of secure app development and operational quality assurance checks. In addition to that, selecting the right DevOps tools for an IoT platform can help overcome challenges in creating and pushing applications and firmware updates to large numbers of devices, as well as monitoring and infrastructure provisioning on-demand. Dr. Vamsi Mohan Vandrangi is going to discuss more details on "Securing Your IoT Applications with DevOps" and explain the step-by-step approach of DevOps, CI/CD pipelines for IoT platform development. He will also talk about the real-time challenges in Internet of Things projects.
See publication
Tags: IoT
World Developers & Selenium Summit
1.21GWS
November 10, 2022
“The World Developers And Selenium Summit, 2022, India” Program was curated based on guidelines from industry experts.
See publication
Tags: Digital Transformation
 Speaker: Open Source Summit Europe 2022
Speaker: Open Source Summit Europe 2022
The Linux Foundation
October 15, 2022
Earners of this badge are speakers, selected by The Linux Foundation, who have provided thought-leadership and shared best practices with attendees during their talk(s) at Open Source Summit Europe 2022.
See publication
Tags: AI, Open Source
 Open Source Summit 2021
Open Source Summit 2021
The Linux Foundation
September 27, 2021
The Linux Foundation awarded this Speaker badge for providing thought leadership and sharing best practises with global professionals during a talk(s) at Open Source Summit 2021. Dr. Vamsi Mohan is an Open Source Subject Matter Expert (SMEs) on the topic(s) presented.
Subject Matter Expert in Open Source, Thought Leadership
See publication
Tags: Digital Transformation, Open Source
The-Cyber-Security-Summit-Bangalore-2020
Unicom
March 06, 2020
Cyber Security Practitioners face many trials and tribulations as they protect and defend their organizations. To seek the best possible protection, they should have well understanding of the threats, which may cause the greatest risk and how to address them proactively. This will enable a quicker and more cohesive response to incidents. Mr. Vamsi Mohan Vandrangi is going to speak more on "Need for Threat Intelligence & How to Operationalize it for your Organisation". At the event, he will talk on the challenges, how to put threat intelligence to work via automated processes.
See publication
Tags: Cybersecurity, Data Center, Digital Transformation
Selenium Day conference 2020
1.21GWS
January 31, 2020
The IT frameworks are getting changed drastically. Software Industry has already in transition from Monolithic frameworks to Microservices frameworks. In this Microservices transformation, Is the traditional way of testing is still valid? How do we test the Microservices? Mr. Vamsi Mohan is going to speak more on "Testing for Microservices". At the event, he will discuss on several examples of Microservices testing strategies, best practices and the open source tools for Microservices testing.
See publication
Tags: Digital Transformation, Emerging Technology, Innovation
Digital Transformation Summit for Managers
1point21gws
August 29, 2019
The financial technology (Fintech) is at a tipping point—either disrupt or get disrupted. As startups and technology firms entice new and challenging customers, those that demand customized and targeted experiences, how will the industry as a whole compete and imbibe intelligence to the existing processes? It is time for migrating from the RPA (Robotic Process Automation) to IPA (Intelligent Process Automation)
Robotic Process automation offers considerable potential for addressing the key pain points in the traditional Fintech system of repetitive tasks. However, there is a limitation to the usability and impact of robots. IPA can address the limitations of current RPA through leveraging Machine Learning, Natural Language Processing and other AI capabilities. IPA choreographs connections among the systems and people, automates structured tasks, and generates intelligence from process execution.
IPA is an emerging set of new technologies that combines fundamental process redesign with robotic process automation, artificial intelligence and machine learning. Intelligent Process Automation is the next wave of Fintech efficiency and the future of automation to a point towards the confluence of enterprise systems and intelligent automation.
See publication
Tags: Digital Transformation, Emerging Technology, Leadership

 Quantum Computing for Business Leaders
Quantum Computing for Business Leaders
 https://medium.com/@vamsi-mohan/revolutionizing-quantum-computing-with-web-services-ee77860123f9
https://medium.com/@vamsi-mohan/revolutionizing-quantum-computing-with-web-services-ee77860123f9
 Advancing Quantum Computing through Industry-Academia Collaboration
Advancing Quantum Computing through Industry-Academia Collaboration
 Hybrid Quantum Computing: Are You Prepared for the Next Technological Shift?
Hybrid Quantum Computing: Are You Prepared for the Next Technological Shift?
 New Methods for Estimating Quantum Computing Requirements
New Methods for Estimating Quantum Computing Requirements
 Fostering the human–machine alliance
Fostering the human–machine alliance
 Quantum Cloud Computing Platforms
Quantum Cloud Computing Platforms
 Software modernization to embrace quantum technology
Software modernization to embrace quantum technology
 Interpolation for Datasets
Interpolation for Datasets
 A future reality - Hackers attacking human memories
A future reality - Hackers attacking human memories
 AI is the future strategy of Enterprises
AI is the future strategy of Enterprises
 Top 50 Global Technology Professional Award
Top 50 Global Technology Professional Award
 Need for Threat Intelligence & How to Operationalize it for your Organisation
Need for Threat Intelligence & How to Operationalize it for your Organisation
 6th World Test Engineering Summit - Thought Leadership Honor
6th World Test Engineering Summit - Thought Leadership Honor
 SECURING YOUR IOT APPLICATIONS WITH DEVOPS
SECURING YOUR IOT APPLICATIONS WITH DEVOPS
 Speaker: Open Source Summit Europe 2022
Speaker: Open Source Summit Europe 2022
 Open Source Summit 2021
Open Source Summit 2021
 Testing Microservices
Testing Microservices
 Digital Customer Experience
Digital Customer Experience